
Introduction
Zero Trust Architecture is a method of protecting computer systems where no user or device is automatically trusted. Every request to access a system is subject to careful verification, no matter where the request originates. Rather than assuming that someone inside a protected network is safe, this method asks each person or piece of equipment to prove their identity and meet all safety requirements at every access point. The idea is not new, but recent events and experiences in data security have led organizations to adopt this way of thinking. Over time, many security teams have realized that the old mindset of an open internal environment simply leaves room for breaches.
Zero Trust Architecture is a security model that requires every user, device, and request to be verified continuously, regardless of network location. It replaces traditional perimeter-based security by enforcing strict identity checks, device health validation, network segmentation, and constant monitoring to limit lateral movement and reduce breach impact. Organisations adopt Zero Trust Architecture to secure modern, distributed systems, support remote work, and protect sensitive data across cloud and on-premises environments.
Historical Overview
In earlier computer systems, security was built on a simple assumption: once a user was allowed into a system through a central gateway, they could access many sensitive parts without further checks. This method worked well when systems were isolated and used only a few trusted devices. However, as systems grew more interconnected and influenced by remote work and cloud services, attackers found new ways to get past a single line of protection. As a result, the original vision of a hard outer wall protecting a soft inner core became outdated for many organizations.
Experienced security teams watched as attackers moved from one part of a network to another after breaching a single entry point. With growing evidence that relying on one gate could expose large areas of data, many professionals began to question long-held practices. Instead, they started to apply the idea that every access request must receive its own check. The result is a system where no area of work, whether inside a corporate building or accessed from a remote location, is ever left unguarded.
Concepts of Zero Trust Architecture
Zero Trust Architecture is based on the belief that every request to access information must be verified no matter who, what, or where it comes from. This method treats every access attempt as if it were coming from outside, whether the user is within a normally safe network or is working remotely. A useful analogy is a large facility in which every room has its own secure lock. Even if someone presents an identification badge at the entrance, every door inside the building requires its own check before granting access.
One important idea in Zero Trust is the verification of identity at each step. Whether the system asks for a password, a unique code sent to a phone, or a fingerprint, the goal is to ensure that only authorized individuals gain entry. In tandem with verifying identity, the system also checks the state of the device in use. Is the computer up to date with its software? Has it installed the latest patches? These checks help to ensure that devices themselves are not compromised.
Because no access is ever taken for granted, the approach also considers the context of every request. Information such as the location of access, the time of the request, and even past activity patterns can all guide the decision on whether to grant access or to apply additional checks. In this way, the system maintains a watchful eye over every access attempt, treating each as a fresh event that must meet all safety requirements.
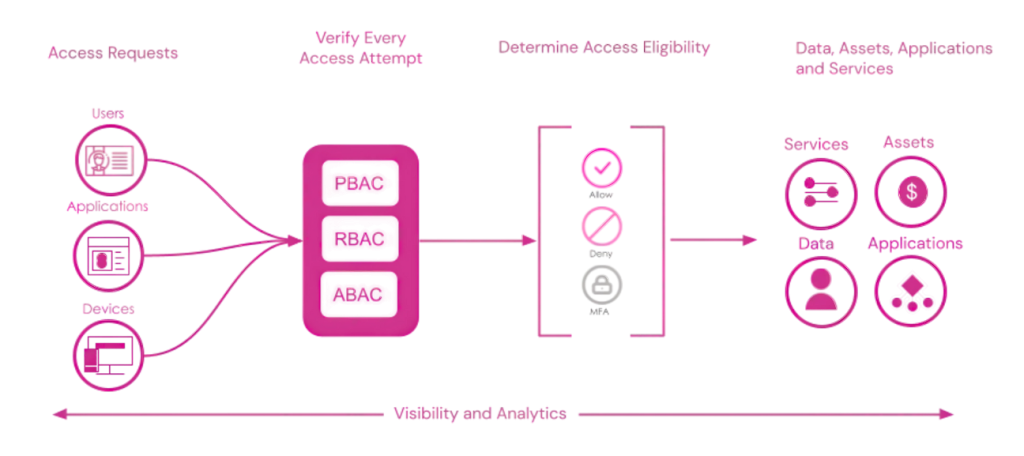
Technical Components
A Zero Trust system is built from a collection of technical components that work together to check every access request. First, strong identity verification methods are used. This may mean asking a user to supply not only a standard password but also a secondary form of verification such as a generated code or biometric data. Each of these methods makes it harder for someone to use a stolen credential without further evidence of identity.
Next, the health of every device plays an important role. Devices must meet set requirements before being allowed to connect. The system may check that a computer has the latest software updates installed or that a mobile device has proper security settings enabled. The system reduces the chance that vulnerabilities in outdated software might be exploited.
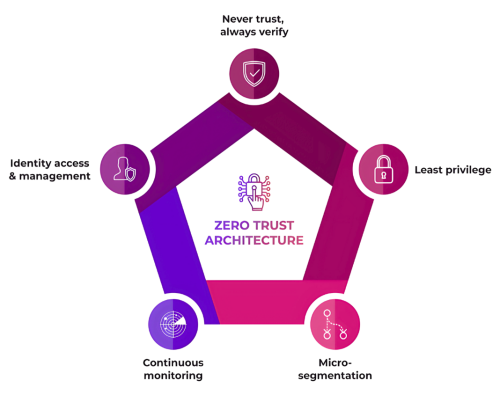
Network segmentation is another technical component used in this approach. Instead of a single, open network where all systems reside, data and applications are split into smaller zones. Each zone has its own set of rules and checks so that even if an attacker manages to get in, their reach is limited. In addition, data flowing between these zones is often encrypted so that even if it is intercepted, the information remains unreadable without proper decryption keys.
Finally, continuous monitoring resolves uncertainties by recording each access event. The system keeps detailed logs of who accesses which resource and when. These records not only help in immediate security checks but later become a valuable tool for detecting any unusual patterns. When the behavior of a user or device begins to stray from the normal pattern, the system may trigger an alert or decide to pause access until further verification occurs.
Implementation and Integration
Moving to a Zero Trust approach requires careful planning and a step-by-step rework of existing systems. Organizations typically begin by mapping out every asset they wish to protect. This involves understanding all the points where data is stored, transferred, or processed. With a clear picture of these assets, decision-makers can define which parts of the system require the highest level of verification.
Once assets are mapped, a set of policies is put in place that dictates the conditions under which access is allowed. Instead of blanket access rights, users and devices are granted permission only when they meet all defined criteria. For example, a system might require that a user not only logs in with the correct credentials but also confirms that the device is in a safe state and that the access request comes from an expected location or device type.
Such policies are usually applied first to the most sensitive areas. As organizations gain confidence in their new safeguards, these policies are expanded gradually across the entire network. This careful rollout allows IT teams to spot any issues early and adjust procedures to best fit the needs of both the system and its users.
Integrating Zero Trust into existing structures can require updating or reworking older systems so that they cooperate with the new rules. Sometimes software must be updated to allow for real-time checks, while other times new devices and services need to be chosen that support these ongoing verifications. This process, while significant, allows organizations to create a safety net where every interaction is recorded and carefully reviewed.
Throughout this transformation, training and clear documentation play an important role. All users in the organization—from executives to front-line staff—should gain a clear understanding of how access requests are handled and why extra checks are necessary. The result is a shared awareness that every action is part of a larger framework designed to protect sensitive data.
Applications of Zero Trust Architecture
The benefits of Zero Trust Architecture become apparent in everyday applications. In the financial sector, for example, client records and sensitive transactions are guarded not only by secure firewalls but by detailed checks at every point of access. An employee in a bank might be allowed to view general information; however, every request to access a detailed record requires a separate review. This constant checking helps prevent a single breach from opening the door to wide-spread access to client data.
Healthcare institutions also apply these principles. Patient data is one of the most sensitive types of information, and in many hospitals and clinics, strict checks are applied every time a record is accessed. A doctor using a tablet in an examination room must prove that their device is secure and that they have permission to view the record at that specific moment. If the system detects an unexpected change or a device that does not meet upgraded safety measures, it may require further verification or block the request entirely. This method helps keep patient information safe even as the tools used in healthcare become more distributed and connected.
Large organizations with remote workers have also found that Zero Trust Architecture helps create a more even and secure environment. Whether a user is logging in from an office computer or a home device, the same strict checks apply. This consistent method removes any assumption of safety based solely on location. Distributed systems and cloud-based services benefit from this approach because every access attempt, regardless of its origin, is treated as if it were coming from outside the organization. When a remote worker logs in from a new location, they are asked to verify their identity in the same way as someone in the office. This practice reduces the risk that a breach in one area will spread to other parts of the network.
Many companies have recognized the need for tools that support these careful checks, and vendors are offering advanced services that align well with Zero Trust Architecture. At X-PHY, we have designed systems that support continuous verification for both users and devices. Our products provide modules that monitor device safety and record every access attempt in a centralized log. These systems seamlessly integrate with older technologies while improving overall security.
Policy and Operational Guidance
A shift to Zero Trust Architecture often requires new policies and operational practices. Every part of the organization must work together to establish clear guidelines that describe how and when access should be granted. Written policies help break down the many tasks involved and allow each team—from security to IT support—to understand their role in protecting data.
These policies define what it means for a device to be safe, what a valid access request looks like, and the steps to be taken when any anomaly is observed. For example, a policy might require that an employee who logs in using a mobile device must also complete a verification step that checks for any irregular activity in the device’s safety status. When an operator views these policies as part of their regular work routine, the organization builds a culture in which everyone understands the value of each access check.

