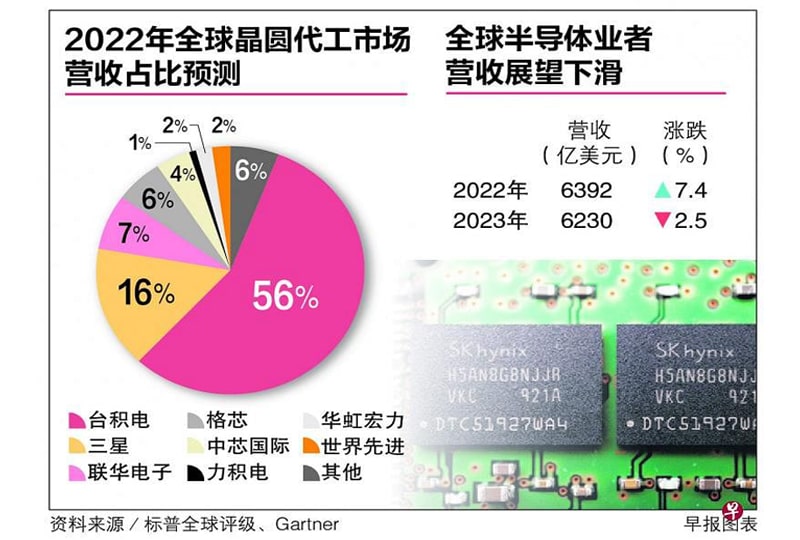
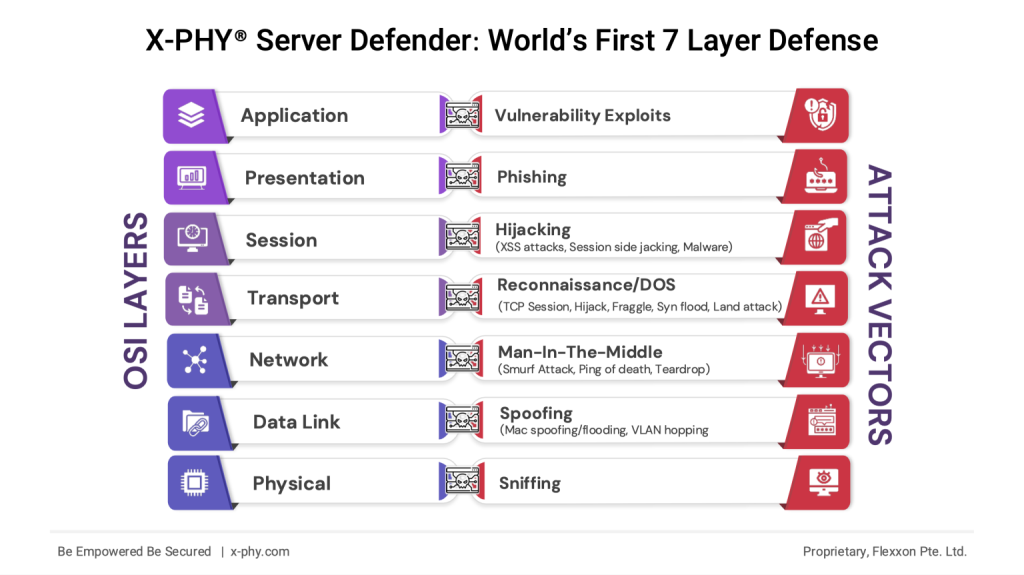
Understanding the OSI Model’s Role in Network Security
Network security requires a deep understanding of how systems communicate and where vulnerabilities exist. The Open Systems Interconnection (OSI) model is the foundation for understanding these communication pathways and the security challenges they face.
The OSI model, developed by the International Standards Organization (ISO), defines seven distinct layers that enable computer systems to communicate over networks. Each layer performs specific functions and interacts with adjacent layers, creating a structured approach to network communications. This layered architecture helps identify security vulnerabilities and implement targeted protection measures.
The Seven Layers and Their Security Challenges
Physical Layer (Layer 1): The Foundation of Network Security
At the most basic level, the physical layer handles the transmission of raw binary data through hardware components like cables, switches, and network cards. This layer faces direct threats from physical tampering, wiretapping, and electromagnetic interference.
Hardware-based security measures prove essential here. Our hardware-embedded solutions provide continuous protection against physical attacks. Organizations create a strong first line of defense against unauthorized physical access and tampering attempts by implementing security at the hardware level.
Data Link Layer (Layer 2): Securing Frame Transmission
The data link layer packages raw bits into frames and ensures error-free data transfer between directly connected nodes. Common attacks at this layer include MAC spoofing, ARP poisoning, and switch port attacks. These threats can compromise network integrity and lead to unauthorized access.
Network Layer (Layer 3): Protection Against Routing Attacks
Responsible for packet routing and addressing, the network layer faces threats like IP spoofing, DDoS attacks, and route poisoning. These attacks can disrupt network operations and compromise data integrity. Our hardware-based security implements real-time monitoring and filtering at the network layer. The system analyzes packet patterns and blocks suspicious traffic before it can impact network operations.
Transport Layer (Layer 4): Defending Against Connection Attacks
The transport layer ensures reliable data delivery and manages error recovery. It’s vulnerable to TCP SYN floods, session hijacking, and port scanning attacks. These threats can overwhelm network resources and disrupt legitimate communications.
Hardware-level security solutions provide faster processing for threat detection and response. Our zero-trust architecture validates every connection attempt, preventing unauthorized access and protecting against transport layer attacks.
Session Layer (Layer 5): Maintaining Secure Communications
Managing communication sessions between applications, this layer faces session hijacking and replay attacks. Attackers can intercept and take control of established sessions to gain unauthorized access.
Presentation Layer (Layer 6): Protecting Data Translation
The presentation layer handles data formatting, encryption, and compression. It’s susceptible to malware injection and code exploitation attacks. These threats can compromise data confidentiality and integrity.
Hardware-based encryption and decryption modules provide superior protection for data processing at this layer.
Application Layer (Layer 7): Securing End-User Services
As the interface for end-user services, the application layer faces numerous threats, including SQL injection, phishing, and malware distribution. These attacks target the user-facing components of network applications.
X-PHY®’s comprehensive security approach includes application-layer protection through hardware-accelerated scanning and filtering. This ensures threats are stopped before they reach end-user applications.
Advanced Persistent Threats Across Multiple Layers
Modern cyber attacks often target multiple OSI layers simultaneously. Advanced Persistent Threats (APTs) use sophisticated techniques to breach networks and maintain long-term access. These attacks require comprehensive security solutions that protect all layers of the network stack.
Our hardware-based security provides unified protection across all OSI layers. The system’s AI-powered technology monitors and correlates activities across layers to identify and block complex attack patterns.
Hardware-Based Security: A Superior Approach
Traditional software-based security solutions operate with inherent limitations. They consume significant system resources and remain vulnerable to software-based attacks. Hardware-based security addresses these shortcomings by:
- Processing security operations directly in hardware components, reducing system overhead
- Providing tamper-resistant protection against physical and logical attacks
- Implementing real-time monitoring and response capabilities
- Ensuring consistent protection without regular updates or patches
Our solutions exemplify these advantages through features like:
- Hardware-embedded AI that monitors system behavior
- Real-time threat detection and response
- Zero-trust security implementation at the hardware level
- Automatic protection against known and unknown threats
Industry-Specific Protection Requirements
Different sectors face unique security challenges that demand specialized protection approaches. Healthcare organizations must protect patient data while maintaining regulation compliance. Financial institutions require robust security for transaction data and customer information. Our zero-trust architecture provides the necessary protection while maintaining system performance and regulatory compliance.
Best Practices for Comprehensive OSI Layer Security
Organizations should implement a multi-layered security strategy that includes:
- Hardware-based security solutions at each OSI layer
- Network segmentation to limit attack spread
- Regular security assessments and testing
- Encrypted communications for sensitive data Comprehensive backup and recovery systems
Our hardware security solutions support these best practices through built-in features and capabilities that protect each OSI layer. The system’s AI technology adapts to new threats while maintaining consistent protection levels.
The Future of Network Security
As cyber threats become more sophisticated, hardware-based security solutions will play an increasingly important role in protecting network communications. X-PHY® continues to advance hardware security technology through AI-embedded security systems. Organizations that implement hardware-based security solutions position themselves to meet current and future security challenges.