Medusa is a Ransomware-as-a-Service (RaaS) operation that has been active since June 2021, impacting over 300 victims by March 2025. The RaaS model allows the developers to “lease out” ransomware tools to affiliates, who then launch attacks in exchange for a percentage of the ransom paid. When it was first reported in 2021, Medusa was run by a centralized developer team, but over time, it evolved into a hybrid model, where affiliates carried out attacks, with developers managing core operations, such as ransom negotiations.
Unlike other types of ransomware that simply encrypt data and demand ransom payment, the group operates under a double-extortion model, where, in addition to encrypting data and demanding ransom payment, they also threaten to publish exfiltrated data if payment is not made. The threat to publish exfiltrated data is facilitated by their public leak site called Medusa Blog, where the group shames non-paying victims by releasing stolen files.
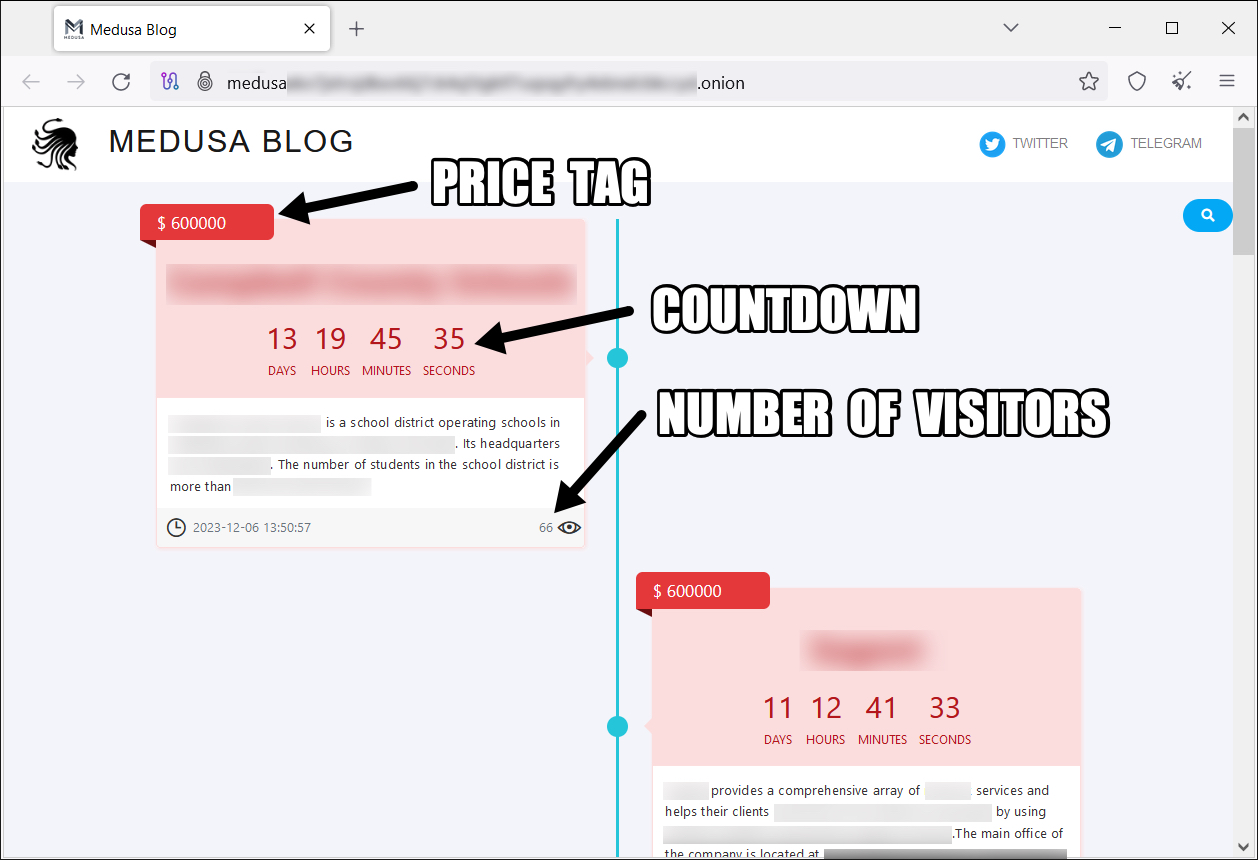
Medusa Blog
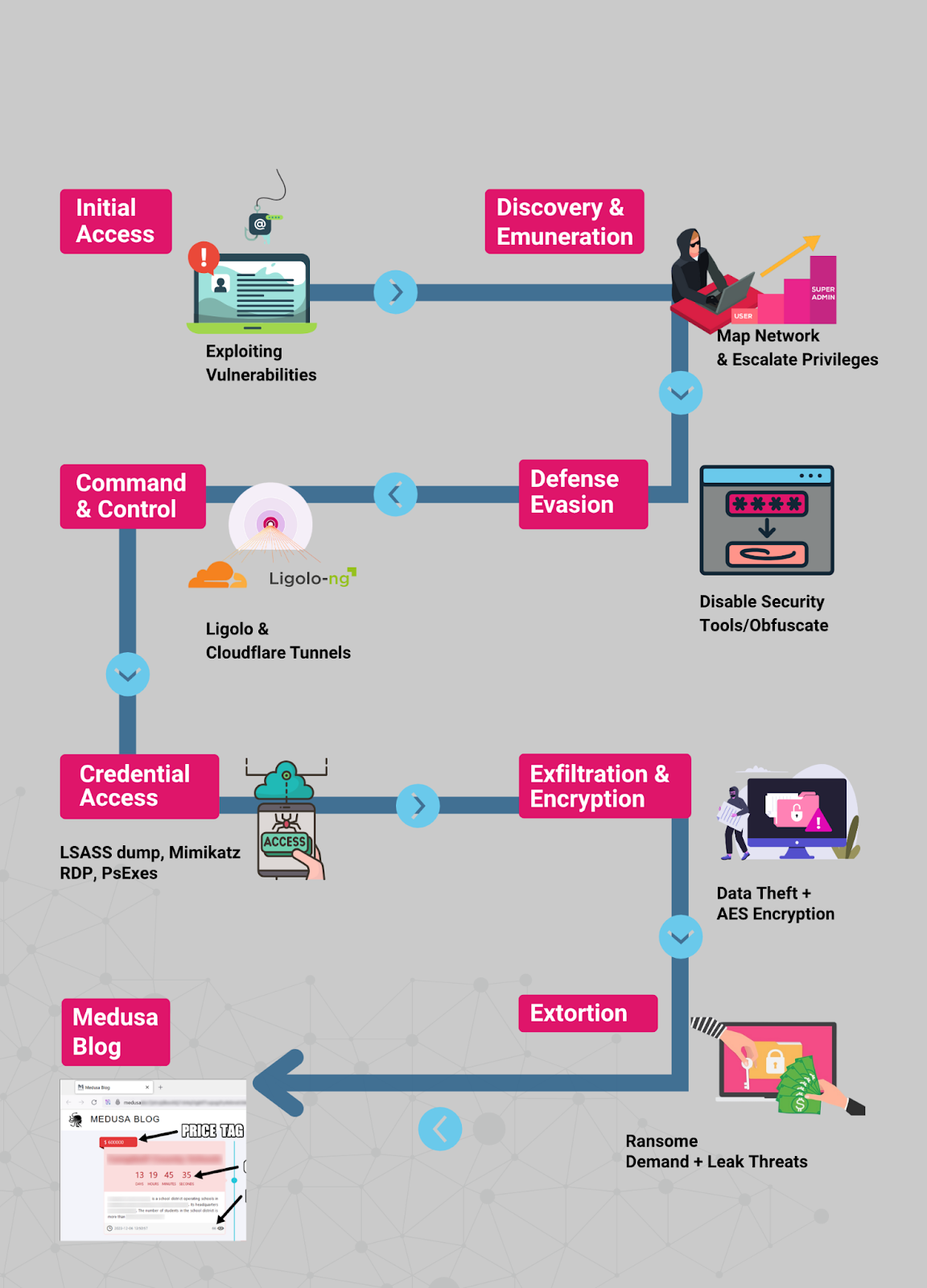
I. Initial Access
Medusa developers typically recruit initial access brokers (IABs) in cybercriminal forums and marketplaces. The affiliates are offered a percentage of the ransom paid on successful attacks with the opportunity to work exclusively for Medusa. Medusa affiliates are known to utilize phishing campaigns and the exploitation of unpatched software vulnerabilities to gain initial access into the targeted organizations’ networks.
Phishing Campaigns
The phishing campaign run by the affiliates is meant to steal credentials or trick users into executing malicious payloads. They achieve this by sending deceptive emails tailored to lure unsuspecting users by impersonating trusted parties such as IT departments or HR. The emails either contain malicious attachments, prompt users to enter login credentials, or trick them into running scripts. A successful phishing campaign is marked by the adversaries gaining access to critical credentials and establishing an initial foothold when the victim executes malware. Once access is achieved, Medusa affiliates quickly escalate privileges and move laterally.
Exploitation of Unpatched Vulnerabilities
Another common technique used by Medusa affiliates to gain initial access is the exploitation of unpatched vulnerabilities in the public-facing applications, such as web apps, VPNs, and remote management tools. The IABs favor this technique because it is silent and does not require user interaction like phishing. Additionally, since they specialize in exploiting such vulnerabilities, they have access to sophisticated tools such as Metasploit that simplify the exploitation process. Some of the Common Vulnerabilities Exposures (CVEs) exploited by the Medusa group include CVE-2024-1709 and CVE-2023-48788. The group exploited CVE-2024-1709, the ScreenConnect Authentication Bypass vulnerability, shortly after its disclosure in early 2024, allowing them to gain full remote access to target systems.
II. Discovery and Enumeration
Once inside the network, the Medusa group takes time to study the environment, learning everything they can. The attackers use this phase to identify high-value targets, map out the network structure, and look for paths to escalate access or spread laterally. This helps them maximize damage and ensure a successful encryption. Common tools and commands used in discovery and enumeration include:
- net group /domain — to list domain user groups
- net localgroup administrators — to reveal local admin accounts
- net view / net use — to map shared drives and folders
- nltest /dclist: — to finds all domain controllers
- tasklist / taskkill — to kill security software
III. Defense Evasion and Obfuscation
After breaching a network and conducting reconnaissance, Medusa ransomware affiliates take deliberate steps to hide their activity and avoid being detected. This allows them to remain undetected long enough to disable security tools, exfiltrate data, and carry out encryption. The attackers achieve this by disabling any security software on the target networks, living off the land (LOTL), renaming payloads, and using a custom loader.
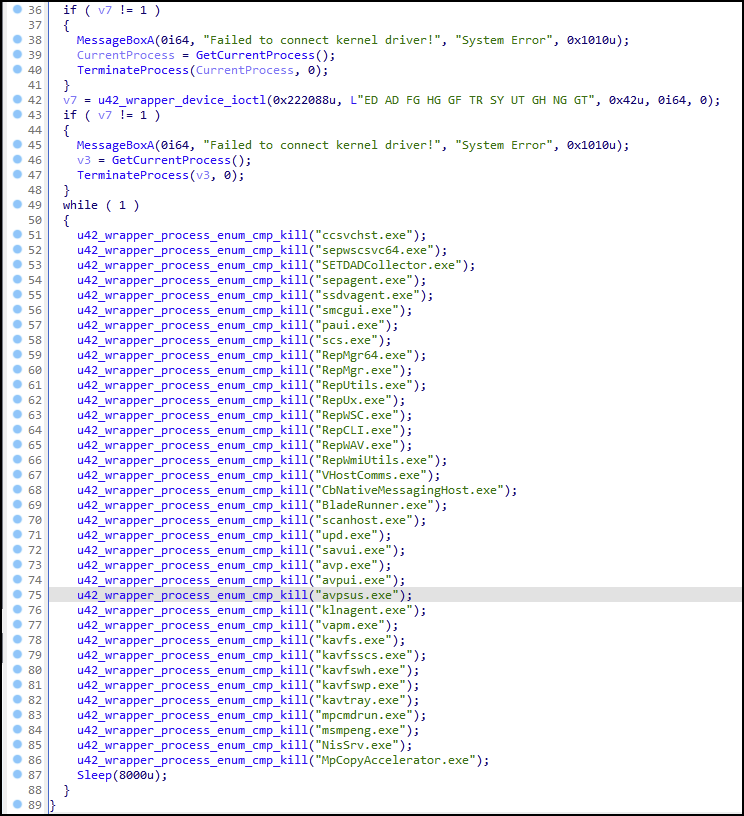
Disabling Security Software
Medusa affiliates disable security tools before encryption to ensure there are no obstacles that could hinder their execution. They commonly use task-killing commands (taskkill /f /im <process>.exe) to stop antivirus, EDR, and backup agents. They target Windows Defender, Sophos, Trend Micro, Veeam, and backup services. They also tamper with registry keys to permanently disable defenses.
Living off the Land (LOTL)
Instead of deploying flashy custom tools (which might trigger alerts), Medusa abuses legitimate Windows utilities to facilitate attacks. For instance, tools like cmd.exe, powershell.exe, and rundll32.exe are used for stealthy system manipulation. This allows them to perform malicious actions using trusted processes, making it less likely to be flagged by EDR.
Renaming Payloads
Attackers rename payloads, encode scripts, or compress files to avoid detection. The common extensions used for these purposes include .zip or .7z extensions. They may also use Base64 encoding, PowerShell obfuscation, or custom packing to avoid signature-based detection.
Using Custom Loader
Medusa ransomware uses a loader that decrypts and runs the main ransomware payload in memory. This reduces disk-based artifacts and bypasses file-based antivirus detection. This enables them to deploy ransomware at scale and operate for days or weeks without being detected.
IV. Command and Control (C2) Setup
Medusa actors use Ligolo and Cloudflared to support command and control (C2) and evade detection. Ligolo is a reverse tunneling tool used to create secure connections between a compromised host and a threat actor’s machine. Cloudflared is used to securely expose applications, services, or servers to the internet via Cloudflare Tunnel without exposing them directly. This gives attackers total control of the battlefield to execute their intentions without being detected.
V. Credential Access & Lateral Movement
This step involves going from a single compromised user to company-wide access and getting more access. An attacker steals one admin credential and turns it into full domain control, going from a single compromised user to company-wide encryption and extortion. This transforms a small compromise into a full-blown network-wide attack, allowing the attackers to encrypt servers, steal data, and increase ransom pressure.
Medusa operators use OS Credential Dumping to extract usernames, passwords, and authentication tokens from compromised machines. OS Credential Dumping allows them to extract usernames and passwords stored in memory on Windows machines from LSASS. LSASS (Local Security Authority Subsystem Service) is a Windows process responsible for storing credentials in memory. When an attacker accesses LSASS, they dump all stored credentials, stealing admin credentials to enable them to spread across the network silently.
Example Workflow:
- Gain admin access to a machine (via phishing or exploit)
- Use procdump to create a memory dump of LSASS
- Transfer the .dmp file to the attacker’s system
- Run Mimikatz to extract usernames, passwords, and hashes
Once attackers have valid credentials, they log in to target systems via Remote Desktop Protocol (RDP) and begin moving from system to system. RDP is often enabled on internal systems, giving attackers a broad attack surface. With administrative rights, they use tools like PsExec or wmic to execute commands and install ransomware remotely across multiple systems at once.
When attackers gain access to the Active Directory domain controller, they essentially own the network. This means that they can create new admin accounts, disable security policies, and push ransomware to every system via Group Policy Objects (GPO). Medusa affiliates often disable logging, tamper with logs, or destroy artifacts to cover their tracks after lateral movement.
VI. Exfiltration and Encryption
Once Medusa ransomware affiliates have gained initial access to the network, moved laterally, and obtained administrator-level access, they initiate the data exfiltration process. This involves copying sensitive data from internal systems to external infrastructure controlled by the attacker. They do this before encryption to maximize pressure on victims. “If you don’t pay, we’ll leak your data” is the central threat of Medusa’s extortion strategy. During the exfiltration process, the attackers target:
- Personally identifiable information (PII)
- Customer and client data
- Financial records
- Legal documents
- Password vaults
Example workflow
1. Attackers bundle stolen files into .zip or .7z archives using tools like WinRAR and 7-Zip.
2. They then use Command-Line Upload Tools like Rclone, MegaCMD, or curl to exfiltrate data to a dedicated attacker-controlled infrastructure
Once data is exfiltrated, Medusa affiliates launch the ransomware payload to encrypt files across the network, rendering them inaccessible to the victim without a decryption key.
How the Medusa Encryption Works
Files on infected machines are encrypted using AES (Advanced Encryption Standard). The AES key is then encrypted with RSA and communicated post-payment. Encrypted files typically have a custom extension, .MEDUSA. Ransom notes (!!!READ_ME_MEDUSA!!!.txt) are dropped in affected directories. The ransom notes contain:
- Instructions for payment
- Links to dark web negotiation sites
- A threat to publish exfiltrated data
VII. Extortion
The Medusa ransom note demands victims make contact within 48 hours via either a Tor browser-based live chat or an end-to-end encrypted instant-messaging platform. If the victim does not respond to the ransom note, Medusa actors will reach out to them directly by phone or email. On Medusa Blog, the attackers display their victims’ ID alongside countdowns to the release of information. They also post ransom demands with direct hyperlinks to Medusa-affiliated cryptocurrency wallets. At this stage, Medusa concurrently advertises the sale of the data to interested parties when the countdown timer ends. Victims can additionally pay $10,000 USD in cryptocurrency to add a day to the countdown timer.
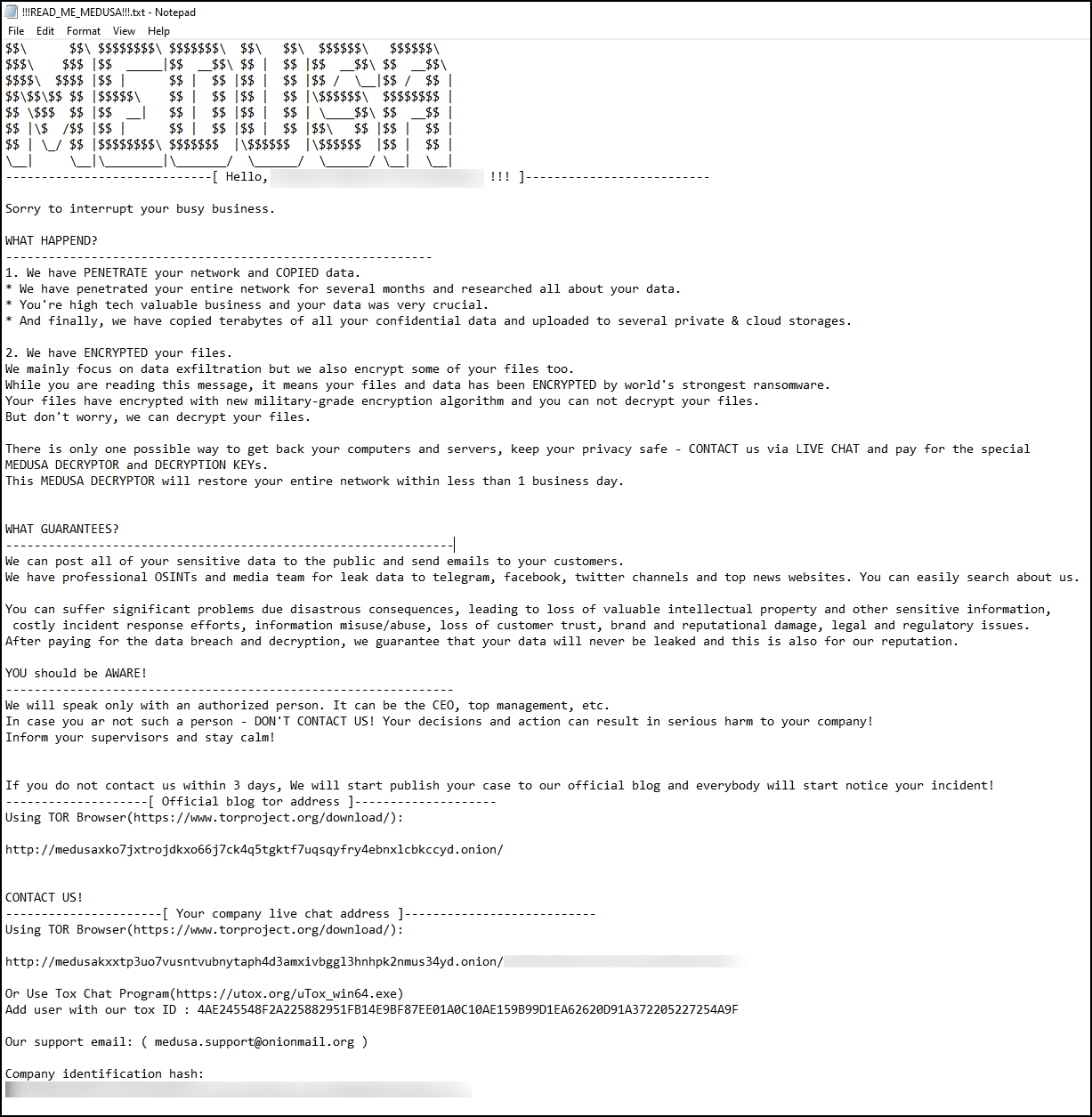
Medusa Ransomware Note
How X-PHY Protects Against Medusa Ransomware
Medusa is a highly sophisticated ransomware that uses phishing, vulnerability exploits, credential theft, and double extortion. Unlike traditional ransomware protection tools that rely heavily on software, X-PHY embeds AI-driven protection directly into the SSD, the ultimate target of ransomware attacks. This means that even when all the other defenses have been bypassed, X-PHY will be the last line of defense standing to protect your data right where it resides.
The critical steps involved in the operations of Medusa group will be instantly detected and subsequently stopped by X-PHY. For instance, the attack involves disabling security tools and exfiltrating sensitive data before commencing encryption. With X-PHY, all these will not be successful because the X-PHY AI is embedded in the hardware, watching out for any abnormal data access patterns and stopping threats before they cause any real harm.
For instance, when Medusa attempts to exfiltrate sensitive data, X-PHY’s AI will detect the abnormally high volume of read operations, triggering SSD lockdown. This will instantly block data transfer and send an alert to the security team about the attempted exfiltration. Blocking the exfiltration phase of Medusa ransomware and locking down the SSD halts the rest of the Medusa processes, thus ensuring the organization’s sensitive data remains protected from the attackers.
The most significant phase of the Medusa ransomware involves encrypting files using AES, appending a .MEDUSA extension, and making the data inaccessible. X-PHY detects ransomware encryption patterns through advanced AI models analyzing how files are accessed and written. Once an attack has been detected, X-PHY interrupts the process of encryption in real time and locks the drive instantly. This will ensure that sensitive data is protected from unauthorized encryption, halting the entire Medusa process.
Why X-PHY is Uniquely Effective Against Medusa
- X-PHY’s hardware-level protection means that the solution doesn’t rely on OS or AV software that Medusa can disable.
- AI-powered anomaly detection gives near 100% detection of unusual patterns even for zero-day threats.
- Immediate response by shutting down and locking the drive prevents encryption and data theft in real time.
- Zero Trust architecture ensures access is always verified.