Understanding the Paths to Cyber Attacks
Businesses all over the world constantly fight off attempts to breach their digital defenses. These attempts are not random – they happen through specific pathways that cybercriminals use to gain unauthorized access to systems and networks. These pathways are known as attack vectors and they are the foundation of most cybersecurity incidents.
Your business’s digital infrastructure is like a fortress. But even a fortress will have gates and windows that soldiers must guard. Likewise, your digital systems have multiple points where attackers might try to exploit. You need to understand these entry points to properly guard them.
Attack vectors are the specific methods cybercriminals use to gain unauthorized access to systems, including phishing, weak credentials, software vulnerabilities, misconfigured cloud services, supply-chain compromises, and insecure IoT devices. Ransomware attack vectors most commonly include email phishing, exploitation of unpatched vulnerabilities, compromised Remote Desktop Protocol (RDP), and malicious software updates. Effective defense requires layered security controls, continuous patching, user awareness training, and real-time monitoring across endpoints, networks, and cloud environments.
The Basics of Attack Vectors
When we talk about attack vectors in cybersecurity, we are referring to the specific methods attackers use to breach a system. Sometimes it’s a simple password guessing, other times its complex technical exploits that take advantage of flaws in the software. What makes attack vectors particularly difficult to defend against is the fact they are many and vary.
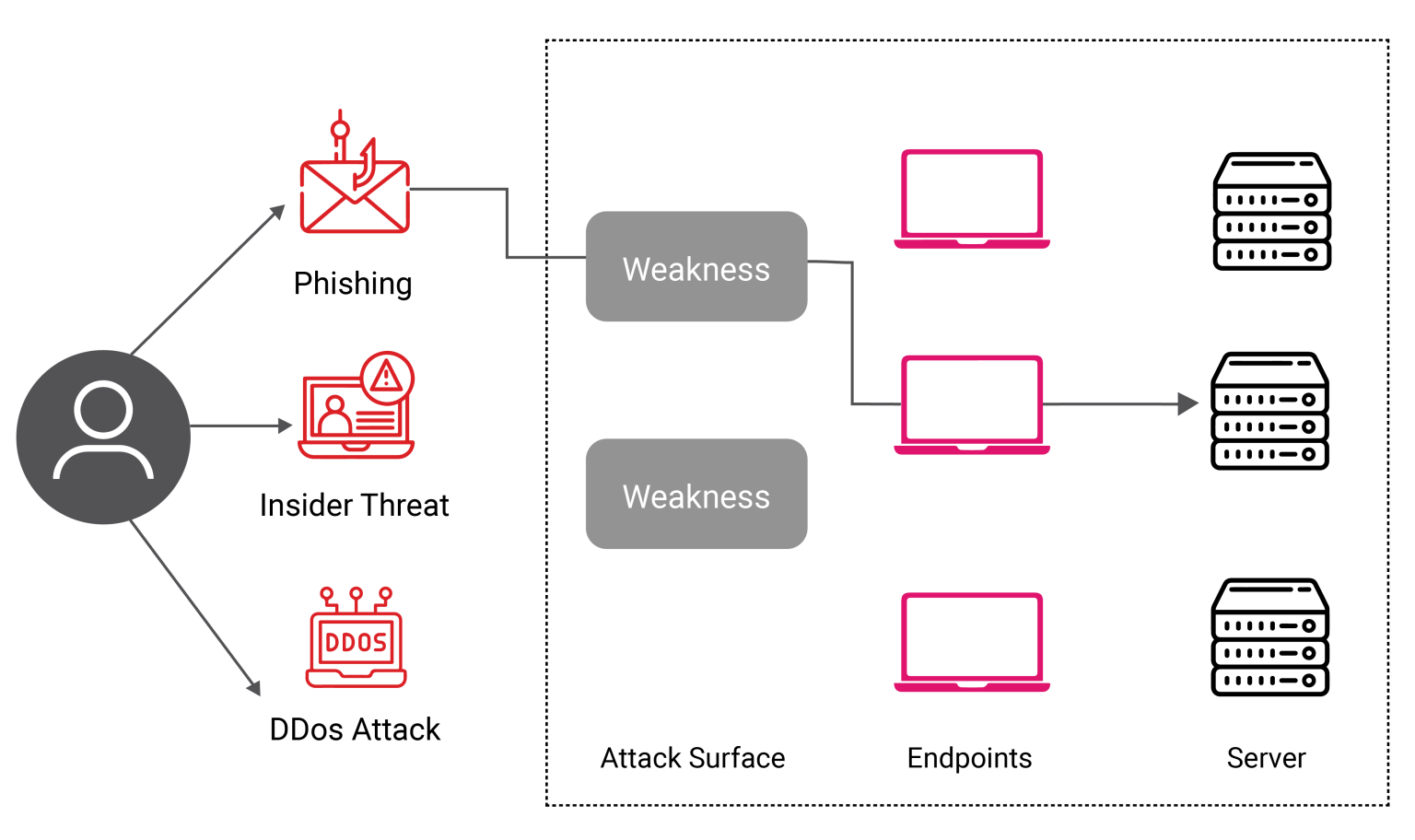
Attackers usually don’t use just one vector – they combine multiple approaches. An attack that start by exploiting the human factor to gain initial access might use technical exploits to go deeper into the network, and then deploy malware to achieve their malicious intentions.
The Human Factor
Most successful attacks often start by targeting people instead of technology. This is called social engineering and these attacks work because they exploit our basic human nature – our tendency to trust, our desire to help, and our occasional lapses in judgment.
An employee receives an urgent email that appears to be from their CEO, asking them to transfer funds or share sensitive information. The email looks legitimate, uses the right language, and creates a sense of urgency. This type of attack succeeds not because of technical sophistication, it just plays on human psychology.
Social engineering takes many forms. Phishing remains the most common, but attackers also use phone calls (vishing), text messages (smishing), and in-person deception.
Technical Attack Vectors
While human-focused attacks remain prevalent, technical attack vectors continue to pose significant risks. Software vulnerabilities is the open window in the fortress.These flaws exist in everything from operating systems to mobile apps, and attackers are constantly searching for new ones to exploit.
Zero-day vulnerabilities is a particularly serious threat. They are previously unknown flaws that give attackers free rein until they’re discovered and patched. Businesses might not know they’re vulnerable until after a breach occurs. This is exactly why we need comprehensive security approaches that don’t rely solely on known threat signatures.

Hardware-Based Security
Traditional security measures focus heavily on software solutions, but recent advances in hardware-based security offer new ways to protect against attack vectors. The X-PHY cyber-secure SSD is a perfect example of this new approach, implementing security at the firmware level and using AI to detect unusual patterns.
Hardware-based security has advantages that software alone can’t match. They are able to monitor data access patterns directly at the hardware level. These systems can also spot malicious behavior without relying on threat signatures or constant updates. They can detect and respond to threats in real-time, even when faced with previously unknown attack methods.
Physical sensors built into devices add another layer of protection. These sensors can detect tampering attempts, unusual environmental changes, and other physical threats that might indicate an attack in progress.
The Supply Chain Challenge
Nowadays businesses cannot operate in isolation – they have to rely on a networks of suppliers, vendors, and partners. Each of this connection is a potential attack vector. Attackers have recognized this vulnerability and increasingly target supply chains to gain access to multiple organizations through a single breach.
The SolarWinds incident demonstrated how supply chain attacks can affect thousands of organizations through a single compromised vendor. Attackers inserted malicious code into legitimate software updates, which were then distributed to customers worldwide. This type of attack is particularly dangerous because it uses trusted channels to spread malware.
The Cloud
As businesses move more and more of their operations to the cloud, new attack vectors are showing up. Cloud services offer tremendous benefits but also create new security challenges. Misconfigured cloud storage, weak API security, and shared infrastructure vulnerabilities are all opportunities for attackers.
Cloud security needs a different mindset than traditional network security. Businesses must secure not only their own infrastructure but also understand how their cloud providers handle security. This shared responsibility model means both parties have critical roles to play in protecting against attacks.
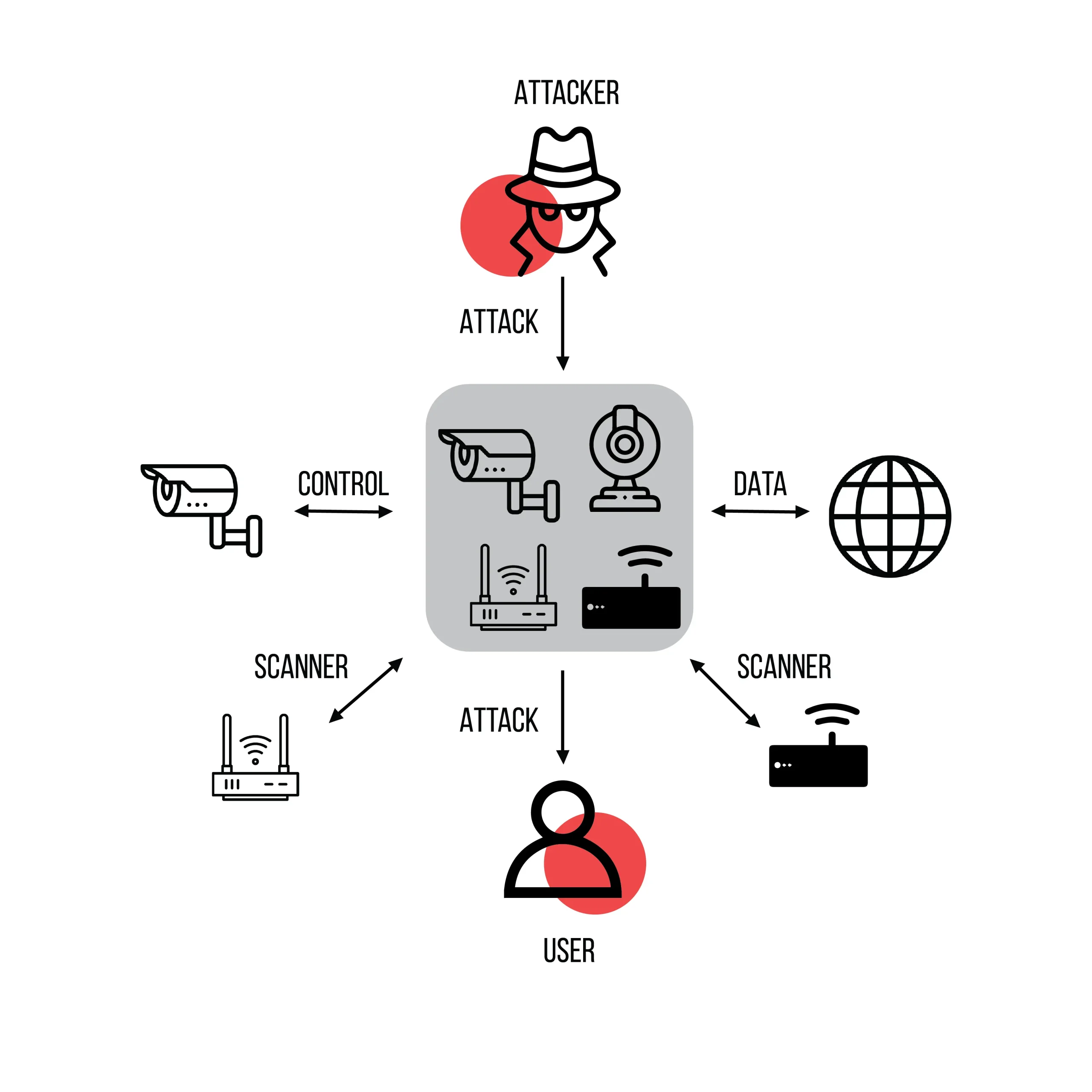
The Internet of Things Expansion
The fact that connected devices are everywhere has created countless new attack vectors. IoT devices lack basic security features and rarely receive updates. Attackers can use these devices as entry points into networks or harness them into botnets for larger attacks.
Businesses and Organizations must consider IoT security as part of their security strategy. This includes maintaining inventories of connected devices, implementing network segmentation to isolate IoT devices, and establishing strict policies for bringing new devices online.
SolarWinds Attack: Play by Play and Lessons Learned https://www.aquasec.com/cloud-native-academy/supply-chain-security/solarwinds-attack/#:~:text=One%20of%20the%20key%20lessons,of%20organizations%20around%20the%20world.
Building Effective Defenses
Protecting against attack vectors needs a multi-layered approach that combines technology, processes, and people. Businesses and organizations need to setup basic security measures while also preparing for advanced attacks.
Technical Measures
Strong technical defenses start with fundamental security controls but must go beyond basics. Organizations should implement:
- Network segmentation to limit the spread of breaches
- Encryption for data at rest and in transit
- Regular system updates and patch management
- Access controls and authentication systems
- Monitoring and logging capabilities Backup and recovery systems
However, technical measures alone aren’t enough. They must be part of a broader security strategy that includes process and policy as well as people and training.
Industry-Specific Considerations
Different industries encounter unique challenges when it comes to attack vectors. Healthcare organizations should prioritize patient data and medical devices. They should maintain quick access to critical information. Financial institutions on the other hand face advance attacks targeting monetary assets. Manufacturing companies must secure industrial control systems without having to disrupt production.
Future Attack Vectors
As technology advances, we will continue to encounter new attack vectors. Artificial intelligence might power more sophisticated attacks that can adapt to defenses in real time. Quantum computing is another looming threat that could change current encryption methods. 5G networks will connect more devices and create more vulnerabilities.
The Role of Artificial Intelligence
Both attackers and defenders both use AI in their efforts. Defensive AI can help identify patterns that might indicate an attack, while offensive AI could help attackers find vulnerabilities or bypass security measures. The our system is a perfect example of how AI can be integrated directly into hardware security measures and used for good.
Measuring and Managing Risk
It might be impossible to eliminate all attack vectors, but you can manage the risks they present. This involves understanding which assets is most valuable and which attack vectors pose the greatest threats. Your risk assessment should consider:
- The value of protected assets
- The likelihood of different types of attacks
- The effectiveness of current security measures
- The cost of additional security controls
- The potential impact of successful attacks
Consequences of Successful Attacks
The consequences of successful attacks through various vectors can be severe. Organizations face financial losses, reputation damage, and operational disruption. Some examples of real-world impacts include. Understanding these impacts helps organizations justify security investments and prioritize defense measures.
- The average total cost of a data breach is $4.88 million. (IBM)
- The average per-record (per capita) cost of a data breach is $165, one dollar higher than 2022 (IBM).
- The average cost of a mega-breach of 50 to 60 million records in 2024 is $375 million, a $43 million increase from 2023 (IBM).
- Annually, hospitals spend 64 percent more on advertising the two years following a breach (American Journal of Managed Care).
Attack vectors is an ongoing challenge for organizations of all sizes. Success in defending against them needs an understanding of how they work and how to implement appropriate security measures.
The key is to take a comprehensive approach that combines technical measures, strong processes, and well-trained people. Businesses that maintain this balance will be best positioned to protect themselves against current and future attack vectors.

