Some attack methods stand out for their straightforward yet effective approach. Brute force attacks perfectly demonstrate this statement. They’re one of the oldest and simplest concepts in hacking. The philosophy is simple – try every possible combination until you find the right one. While this might sound basic, brute force attacks are a serious threat to organizations and individuals.
Brute force attacks are cyberattacks in which attackers systematically try large volumes of password or key combinations to gain unauthorized access to accounts, systems, or encrypted data. Using automated tools and high-speed computing, attackers can test millions to billions of guesses per second, exploiting weak or reused passwords. These attacks commonly lead to data breaches, financial loss, and system compromise when strong authentication controls are not in place.
What Are Brute Force Attacks?
Brute force attacks are methodical attempts to gain unauthorized access to systems by guessing login credentials, encryption keys, or passwords. If a thief tries every possible key combination on a lock – given enough time and attempts, he might eventually find the right one. The difference is that unlike the thief, computers can make thousands or even millions of these attempts per second.
These attacks work because many people and organizations still use weak passwords or don’t implement proper security measures. Even in 2025, “123456” and “password” remain among the most common passwords, making them easy targets for attackers.
The Mechanics Behind Brute Force Attacks
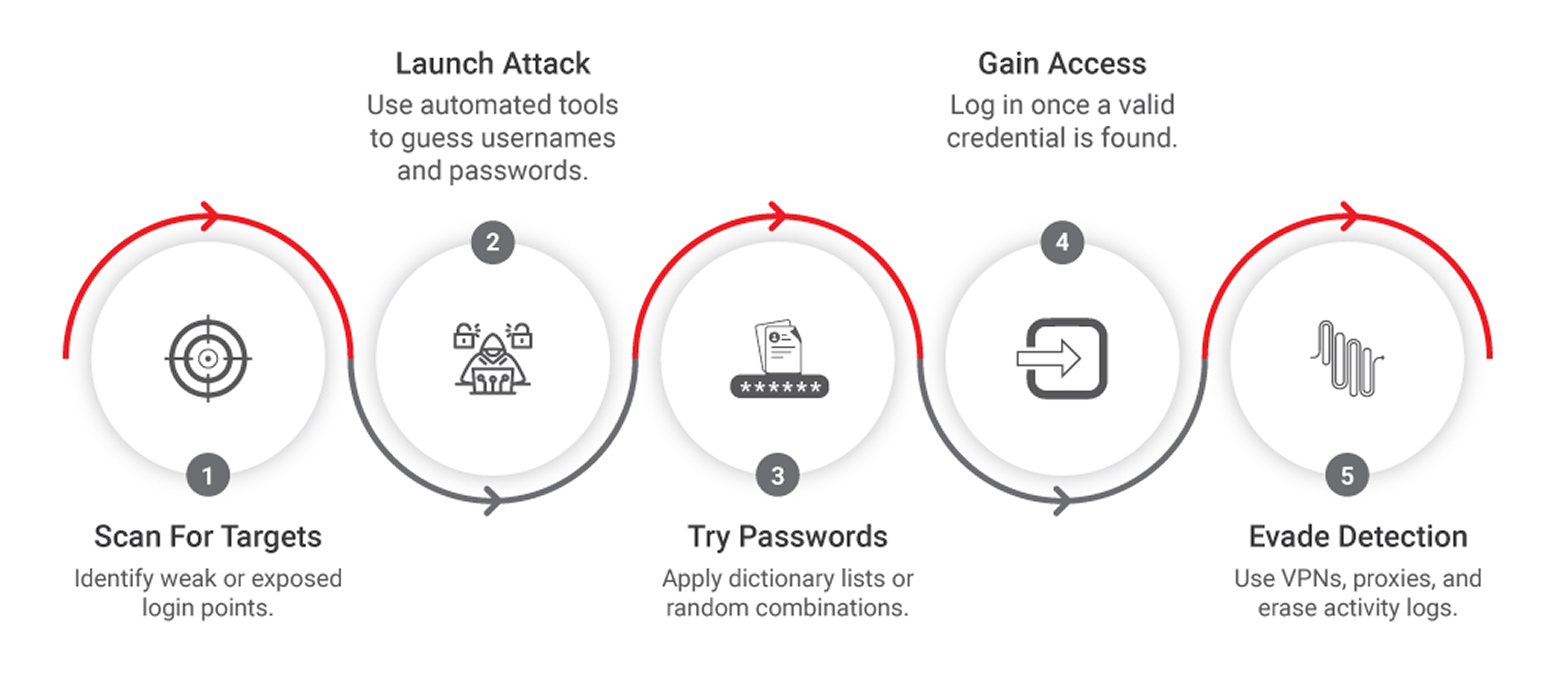
passwords might be cracked in minutes, while complex ones could take years. Back in 2012, a researcher demonstrated the capability to check 350 billion passwords per second using a computer cluster – today’s technology makes this look like child’s play.
Dictionary Attacks
Dictionary attacks are more refined in approach. Instead of trying random combinations, these attacks use common words, phrases, and previously leaked passwords. The method got its name because early versions literally used dictionary words as guesses. Modern dictionary attacks are more sophisticated, they use;
- Common password variations
- Character substitutions (like @ for a, or 1 for i)
- Known password patterns
- Previously leaked credentials
Credential Stuffing
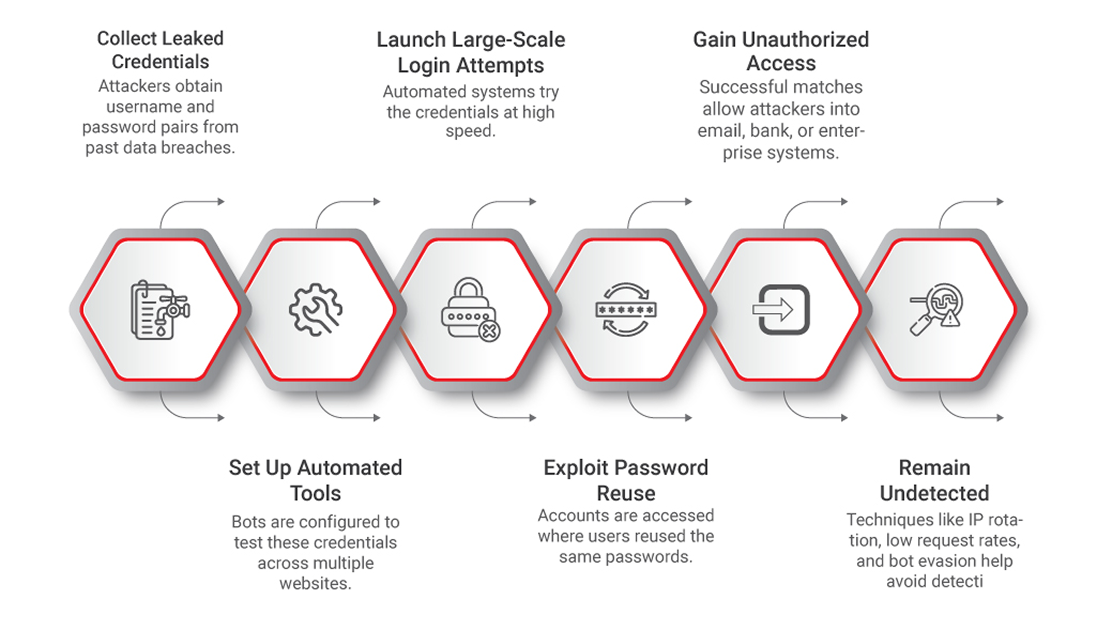
Someone uses the same login details for their email and bank account, compromising one means compromising both. Gaming platforms, media services, and retail websites are frequent targets, but no industry is immune. The low cost of launching these attacks – sometimes as little as $550 – makes them accessible to many bad actors.
Reverse Brute Force Attacks
Unlike traditional approaches where attackers know the username and guess passwords, reverse brute force attacks flip the script. Attackers start with known passwords (often from data breaches) and try to match them to usernames. This method is most effective when targeting common passwords across large user bases.
Hybrid Attacks
Hybrid attacks combine dictionary and brute force methods to create a more efficient approach. They target predictable password patterns, like words followed by numbers. For example, many people add four digits (often a meaningful year) to the end of their password. Hybrid attacks use dictionary words for the main password and then systematically try number combinations at the end.
Password Spraying
This technique takes a different approach from traditional brute force methods. Instead of trying many passwords against one account, password spraying attempts to use a single common password against many accounts. This helps avoid account lockouts and works particularly well against single sign-on systems and cloud applications.
The Tools of the Trade
Modern brute force attacks use sophisticated tools. Many available for free or purchase on the dark web. Some notable examples include:
- Aircrack-ng: Built for Wi-Fi network security testing, it includes tools for monitoring, exporting data, and testing various attack methods.
- John the Ripper: An open-source password recovery tool that works across multiple platforms and can crack various types of password hashes.
- Hashcat: A CPU-based tool that supports multiple attack modes and works across different operating systems.
- THC Hydra: Specializes in cracking network authentication across more than 30 protocols.
Attackers often use botnets – networks of compromised computers – to distribute the computational load and add anonymity to their attacks. This allows them to launch larger-scale attacks without maintaining their own infrastructure.
Why Attackers Use Brute Force Methods
Modern brute force attacks use sophisticated tools. Many available for free or purchase on the dark web. Some notable examples include:
Attackers often use botnets – networks of compromised computers – to distribute the computational load and add anonymity to their attacks. This allows them to launch larger-scale attacks without maintaining their own infrastructure.
| Financial Gain | Data Theft | System Control | Reputation Damage |
Attackers might target financial accounts directly or use compromised accounts for advertising fraud. They might:
| Once inside an account, attackers can steal:
| Successful brute force attacks give attackers control over systems, which they might use to:
| Some attacks aim to harm organizations by:
|
Protection Strategies
Modern password requirements go beyond simple combinations of letters and numbers. A strong password should stretch to at least 12 characters and use a blend of uppercase and lowercase letters, numbers, and special characters. However, length and complexity alone might not guarantee safety. Many users fall into predictable patterns that weaken even complex passwords.
Ensure each account has its own unique password. This practice stops credential stuffing attacks. When you recycle passwords across accounts, one breach will cascade into multiple compromises. System hardening completes this defensive framework. Regular security updates patch vulnerabilities before attackers can exploit them.
Hardware-Based Security
Modern security solutions like the X-PHY implement security at the firmware level. Our devices:
- Monitor data access patterns
- Detect unusual behavior
- Respond to threats in real-time
- Protect against physical tampering
Impact of Brute Force Attacks
$375 million
is the cost of a mega-breach involving
50–60 million records.
Operational Disruption
- System downtime
- Lost productivity
- Recovery costs
- Legal expenses
$4.88 million
is the average cost of a data breach.
Reputation Damage
- Lost customer trust
- Increased marketing costs
- Damaged brand value
- Reduced market share
Conclusion
Protecting ourselves against brute force attacks requires constant vigilance and adaptation. As attack methods become more sophisticated, defense strategies must keep pace.
1 25-GPU cluster cracks every standard Windows password in <6 hours
2 Global Average Cost of a Data Breach Reaches $4.88M in 2023
https://riskandinsurance.com/global-average-cost-of-a-data-breach-reaches-4-88m-in-2023/
3 Data Breach Statistics

