A backdoor attack occurs when attackers create or use hidden entry points to bypass standard security measures and gain unauthorized access to a system or network. Its like a secret entrance to a building that circumvents all security checkpoints. Backdoors allows attackers come and go as they please undetected.
Backdoor attacks occur when attackers create or exploit hidden access points in software, hardware, or networks to bypass normal security controls and maintain unauthorized, long-term access to systems. These attacks are especially dangerous because they often remain undetected while enabling data theft, surveillance, or further malware installation. Effective prevention requires system hardening, continuous monitoring, and strict supply-chain security.
Understanding Backdoor Attacks
Backdoor attacks usually stand out as particularly dangerous when cybersecurity experts discuss system vulnerabilities. This is because they can remain hidden for long periods. Unlike other cyber attacks that might immediately show that there has been a breach, backdoor attacks stay hidden and attackers continue to have access to compromised systems.
A backdoor is a deliberately placed entry point that lets someone bypass all the regular security checks. Once inside, attackers can steal data, install additional malicious software, or simply monitor activities until they decide to act.
How Backdoor Attacks Work
Backdoor attacks function through various methods, but they all share a common objective. To create or exploit hidden access points that let attackers return whenever they want. So, how do these attacks typically unfold:
Initial Access
Attackers first need to establish their backdoor. They might:
- Install malicious software that creates a hidden entrance
- Exploit existing vulnerabilities in systems
- Trick users into installing backdoor programs
- Take advantage of poorly secured remote access tools
Maintaining Access
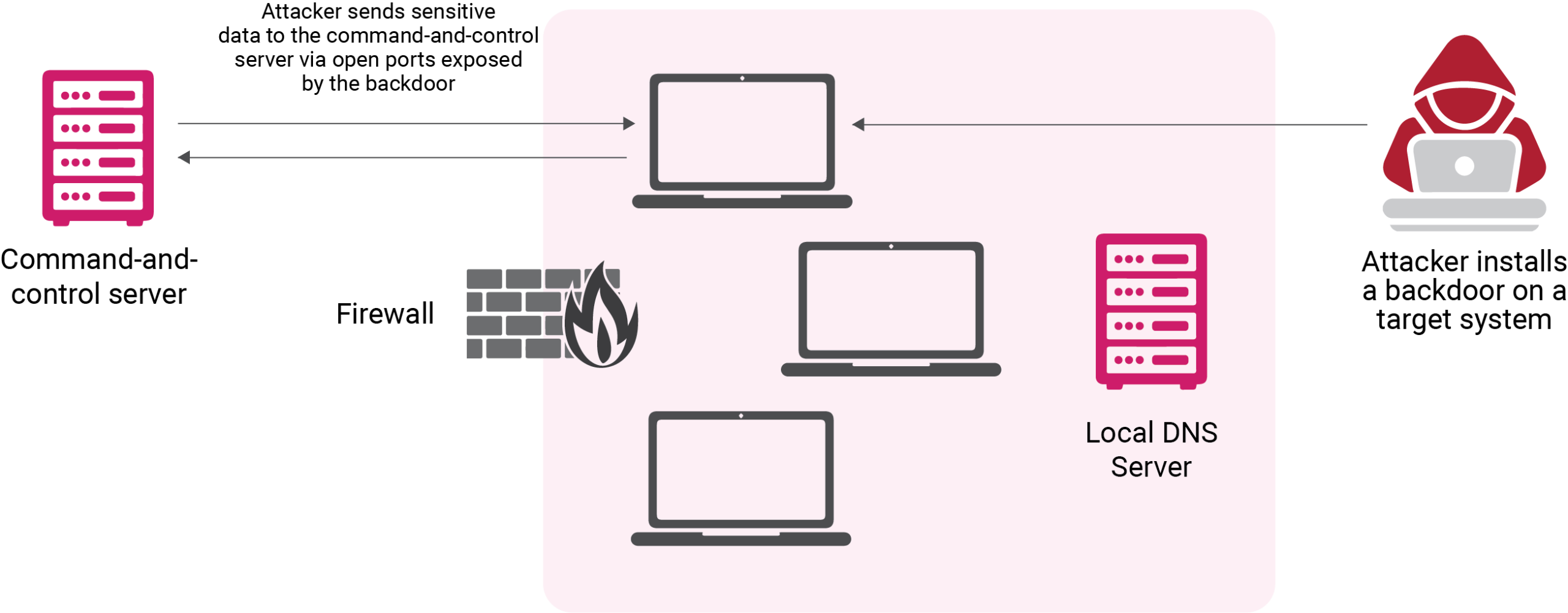
After establishing a backdoor, attackers put all effort into ensuring it stays hidden. They want to exploit the undetected access to the system for as long as possible. One common tactic is to alter system logs and erase any trace of their activities just like a burglar would wipe away fingerprints. They also make their backdoor appear as a normal part of the system. To ensure they don’t lose access if one entry point is discovered, they frequently set up multiple hidden administrator accounts across the system. For more permanent access, they might install rootkits – specialized software that operates at the core of the system.
Types of Backdoor Attacks
Software Backdoors
Software backdoors are the most common types of backdoor attacks. These can exist in applications either by accident through programming oversights or through deliberate insertion. Developers sometimes create backdoors for testing or maintenance but forget to remove them before release. Malicious actors can also insert backdoors by modifying existing software or creating fake versions of legitimate programs.
For example, in 2014, WordPress encountered multiple backdoors hidden within seemingly legitimate plugins. These backdoors contained obfuscated code that created hidden administrator accounts, giving attackers complete control over affected websites.
Hardware Backdoors
Hardware backdoors exist at the physical component level – within processors, chips, or other hardware elements. These backdoors can be extremely hard to detect since they’re built into the physical infrastructure of devices. They might be inserted during manufacturing or through the modification of existing hardware.
The X-PHY cyber-secure SSD offers an interesting contrast here – it uses hardware-level security features to prevent backdoors rather than create them. Its built-in sensors and AI-driven detection help identify and stop unauthorized access attempts at the physical level.
Cryptographic Backdoors
Cryptographic backdoors target the mathematical foundations of security systems. They weaken or bypass encryption by creating deliberate vulnerabilities in cryptographic algorithms. The Dual_EC incident is a notable example – this cryptographic standard contained a suspected backdoor that could potentially allow for the decryption of protected communications.
Developer Backdoors
Sometimes called maintenance hooks, these backdoors are deliberately created by software developers for legitimate purposes like debugging or system maintenance. However, if not properly secured or removed before release, these backdoors can become security risks.
Popular Examples of Backdoor Attacks
The SolarWinds Incident
One of the most significant backdoor attacks occurred through the compromise of SolarWinds’ Orion platform. Attackers inserted malicious code into software updates, creating backdoors in thousands of organizations, including major corporations and government agencies. The attack remained undetected for months and cost SolarWinds approximately $40 million in direct expenses.
C-DATA Device Backdoors
Security researchers discovered multiple backdoors in C-DATA Optical Line Termination devices. These backdoors appeared to be intentionally placed by the vendor, raising serious concerns about supply chain security and trust in hardware manufacturers.
Detection and Prevention:
Identifying Backdoors
Detecting backdoors requires vigilance and systematic monitoring. Watch out for:
- Unusual network traffic patterns
- Unexpected outbound connections
- Strange system behavior or performance changes
- Unauthorized configuration changes
- Mysterious new user accounts
- Unexplained system modifications
Regular security audits and network monitoring help spot these warning signs early. Modern security tools use behavioral analysis to identify suspicious activities that might indicate the presence of a backdoor.
Prevention Strategies:
System Hardening
System hardening is the basics of protection against backdoor attacks. Organizations must take a comprehensive approach by limiting user privileges and maintaining regular security updates.
Any software that can be an entry point should be removed. Network segmentation is another protective layer. It contains any potential breach to a limited area. If we think of it like securing a building, you will need strong locks, regular maintenance, removal of unused entrances, separate secure areas.
Supply Chain Security
Given the rise in supply chain attacks, organizations should:
- Verify the integrity of software and hardware from suppliers
- Implement vendor risk assessment programs
- Use code signing and verification
- Monitor third-party access to systems
Advanced Security Measures
Hardware-based security solutions like X-PHY use AI and physical sensors to detect unauthorized access attempts. Zero-trust security models verify every access attempt, regardless of source and continuous monitoring of systems to watch for suspicious activities.
Backdoor attacks will remain a significant security concern. Organizations must stay informed about new attack methods and defense strategies while maintaining strong basic security practices. Success requires a balanced approach that combines technical solutions, educated users, and effective policies.
Cybersecurity as a field continues to progress, with innovations like hardware-based security solutions offering new ways to protect against these threats. Organizations can better protect themselves against these hidden threats by understanding how they work and implementing appropriate security measures.
2 The Strange Story of Dual_EC_DRBG
https://www.schneier.com/blog/archives/2007/11/the_strange_sto.html
3 SolarWinds hack explained: Everything you need to know
https://www.techtarget.com/whatis/feature/SolarWinds-hack-explained-Everything-you-need-to-know
4 Backdoors Identified in Tens of C-Data Fiber Broadband Devices
https://www.securityweek.com/backdoors-identified-tens-c-data-fiber-broadband-devices/

