Businesses face numerous cybersecurity challenges and the Distributed Denial of Service (DDoS) attack is one of the most disruptive and potentially damaging threats. They can cripple websites, services, and entire networks, causing significant financial losses and damage to reputation. A DDoS attack occurs when an attacker floods a target system with overwhelming traffic, such as a website or network. This traffic exhausts the target’s resources, making it unable to respond to legitimate requests. As a result, the service becomes unavailable to genuine users, hence the term “denial of service.” The “distributed” aspect of a DDoS attack refers to the attack traffic coming from multiple sources, often thousands or even millions of compromised devices. These devices, typically known as a botnet, are ordinary computers, smartphones, or Internet of Things (IoT) devices that have been infected with malware and are under the attacker’s control.
DDoS attacks are cyberattacks in which multiple compromised devices flood a website, server, or network with massive traffic, overwhelming its resources and making services unavailable to legitimate users. These attacks can cause severe financial losses, operational downtime, reputational damage, and are often used to mask data breaches or other malicious activities. Modern DDoS attacks are increasing in scale and sophistication due to IoT botnets and DDoS-for-hire services.
Types of DDoS Attacks
DDoS attacks come in various forms, each targeting different aspects of a network or system:
- Volume-based attacks aim to saturate the target system’s bandwidth. Examples include UDP floods and ICMP floods.
- Protocol attacks exploit weaknesses in network protocols. SYN floods and Ping of Death attacks fall into this category.
- Application layer attacks target specific applications or services, such as HTTP floods or attacks on DNS servers.
- Amplification attacks use techniques to amplify the attack traffic. DNS amplification and NTP amplification are common examples.

The Impact of DDoS Attacks
The consequences of a successful DDoS attack can be severe and far-reaching. Some of the potential impacts include:

Financial losses
Downtime can result in lost sales, productivity, and customer trust. According to a report by Neustar, the average DDoS attack cost for businesses rises to over $2.5 million.

Damage to reputation
Customers and partners may lose confidence in a company's ability to protect their data and maintain services.

Operational disruption
DDoS attacks can halt critical business operations, affecting internal processes and customer-facing services.

Regulatory consequences
Service outages can lead to compliance violations and potential fines in some industries.

Security breaches
DDoS attacks are sometimes used as a smokescreen to distract from other malicious activities, such as data theft or malware insertion.
The Growing Threat of DDoS Attacks
DDoS attacks have become more frequent, sophisticated, and powerful. Several factors contribute to this trend. One of this is the proliferation of IoT devices. This has created a larger pool of potential botnet recruits. Additionally, cheap and easy-to-use tools such as DDoS-for-hire services have lowered the barrier to entry for would-be attackers. According to Netscout’s Threat Intelligence Report, there was a 43% increase in application-layer attacks compared to 2023. It also reported a 55% increase in threats to critical infrastructure sectors over four years.
Notable DDoS Attacks
Several high-profile DDoS attacks have made headlines over the years, demonstrating the potential scale and impact of these threats:
Mirai Botnet Attack (2016)
This attack peaked at 1.1 Tbps and used a botnet of IoT devices to target DNS provider Dyn, disrupting major websites like Twitter, Netflix, and Reddit.
GitHub Attack (2018)
A 1.35 Tbps attack hit the popular code repository, briefly taking it offline.
Amazon Web Services (2020)
AWS mitigated a 2.3 Tbps attack, the largest ever recorded.
Cloudflare’s Largest-Ever DDoS Attack (2024)
Cloudflare reported mitigating the largest-ever publicly disclosed DDoS attack, which peaked at 3.8 Tbps. This attack targeted multiple industries, particularly financial services and telecommunications.

Protecting Against DDoS Attacks
Defending against DDoS attacks requires a multi-layered approach. Some key strategies include:
- Traffic analysis and filtering: Implement systems distinguishing between legitimate and malicious traffic.
- Network architecture design: Distribute resources across multiple data centers and use content delivery networks (CDNs) to absorb traffic spikes.
- Bandwidth over-provisioning: Ensure your network can handle traffic volumes well beyond average.
- DDoS mitigation services: Partner with specialized providers who can detect and mitigate attacks in real time.
- Incident response planning: Develop and regularly test a DDoS response plan to minimize downtime and damage.
- Regular security audits: Identify and address vulnerabilities in your network and applications.
- Employee training: Educate staff about DDoS threats and proper security practices.
While these strategies are important, they often mostly rely on software-based solutions that can be vulnerable to sophisticated attacks. This is where hardware-based security solutions, such as those offered by X-PHY®, can provide an additional layer of protection.
X-PHY® Technology: A Hardware-Based Approach to Cybersecurity
X-PHY® offers a unique approach to cybersecurity that complements traditional DDoS protection methods. X-PHY® provides a defense against various cyber threats by embedding security measures directly into hardware.
Key features of X-PHY®’s technology include:

AI-embedded hardware protection
X-PHY® uses artificial intelligence algorithms built directly into storage devices. This provides real-time threat detection and prevention.

Firmware-based security
X-PHY® creates a much harder barrier for attackers to breach than software-only solutions.

Real-time threat detection
Its AI can identify unusual patterns in data access, potentially catching malicious activities that might slip past network-level DDoS defenses.

Autonomous response
When a threat is detected, it can immediately protect data without human intervention.

Zero-trust architecture
It implements a zero-trust model, continuously verifying every access attempt. This can help prevent lateral movement if an attacker breaches network defenses during a DDoS attack.
How X-PHY® Complements DDoS Protection
While X-PHY® isn’t primarily designed as a DDoS mitigation tool, its capabilities can significantly enhance an organization’s overall security posture, which is important when facing complex cyber threats:
Data protection during attacks:
If a DDoS attack is used as a distraction for data theft attempts, X-PHY® real-time monitoring and protection can safeguard sensitive information.

Endpoint security:
It can protect individual devices that might be targeted as part of a broader attack strategy.

Continuous protection:
Unlike software solutions that might be disabled during a system crash caused by a DDoS attack, X-PHY® hardware-based security remains active.
Case Study: X-PHY® in Action
Consider a scenario where a financial services company faces a sophisticated DDoS attack. The attackers launch a massive volume-based attack on the company’s public-facing websites while simultaneously attempting to exploit the distraction to breach internal systems and steal customer data. The company’s traditional DDoS mitigation service filters out malicious traffic, keeping critical services online. However, the sheer volume of the attack strains the network, slowing down internal systems and creating confusion among IT staff. In this chaos, an attacker attempts to access a customer information database server. This is where X-PHY®’s hardware-based security proves its worth:
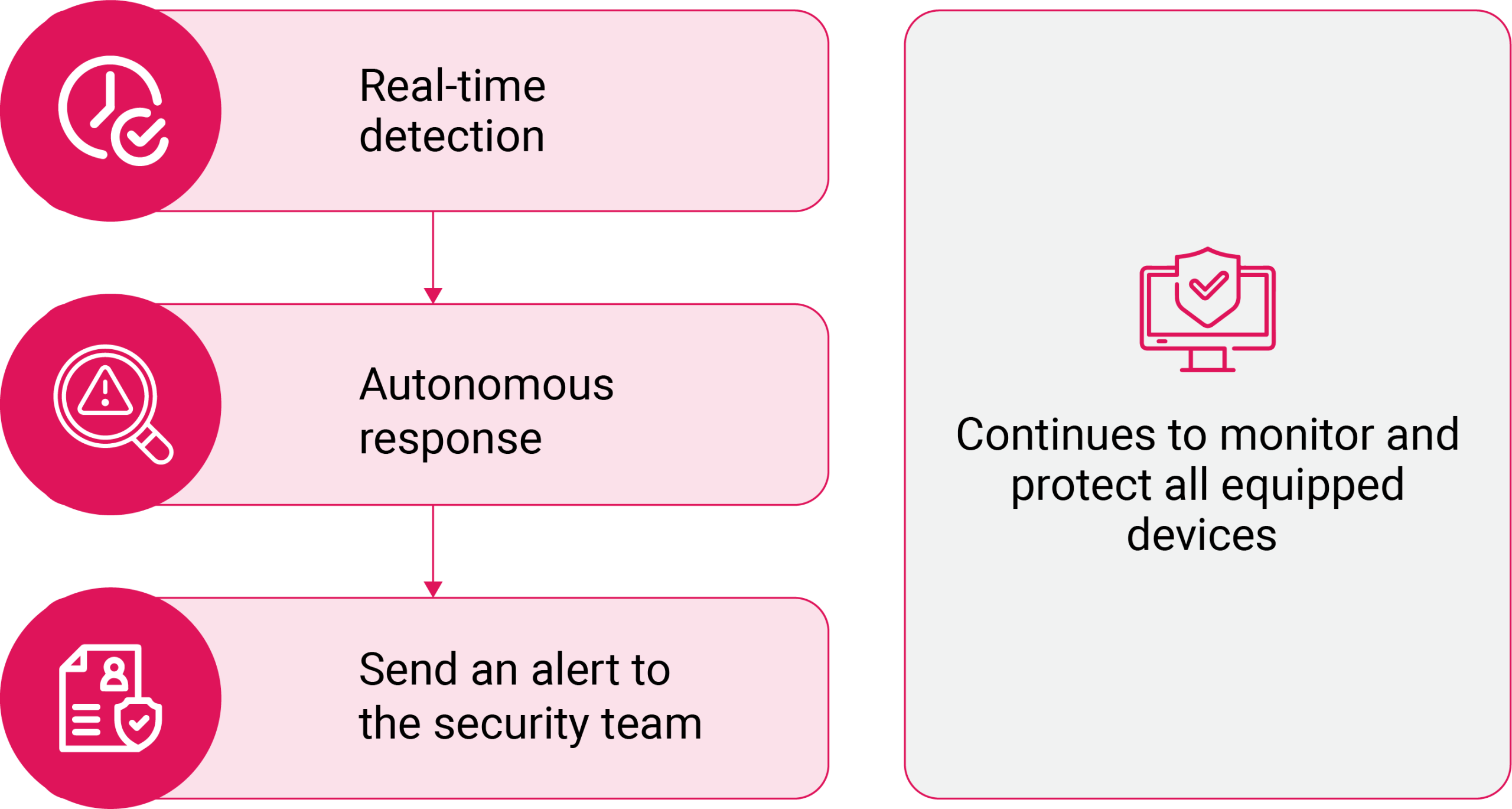
In this scenario, while the DDoS attack caused some disruption, the combination of network-level DDoS mitigation and X-PHY®‘s hardware-based security prevented a potentially catastrophic data breach. DDoS attacks remain a significant threat to businesses of all sizes. As attack methods become more sophisticated, organizations must adopt comprehensive security strategies that protect not just against the DDoS itself but also against accompanying threats that might exploit the chaos caused by an attack.

