The internet introduces risks that can threaten its very existence. Organizations face increasing threats from cybercriminals as they become more dependent on technology. They experience increased system failures and data breaches. This reality has given rise to cyber insurance, a specialized form of coverage that acts as a financial safety net against these risks. Cyber insurance is a specialized insurance product that protects businesses from internet based risks and threats to their information technology infrastructure. It functions a whole lot like property insurance for physical assets, except that it insures online assets, customer data, and business operations from cyber threats. Just like a business wouldn’t operate without fire insurance for its buildings, businesses need protection against online threats that could otherwise lead to devastating losses.
Feature | Traditional Insurance | Cyber Insurance |
Protected Assets |
|
|
Coverage Types |
|
|
Cyber insurance began in the late 1990s, when businesses first started becoming dependent on digital systems. The initial policies were simple and focused primarily on basic data breaches and computer attacks. But as technology continued to advance and these threats became more sophisticated, insurance providers had to expand their coverage to address new types of attacks and their consequences.
A watershed moment in cyber insurance history was the Sony PlayStation Network breach of 2011. The attack exposed 77 million user accounts and cost Sony more than $171 million – none of which was covered by their traditional insurance policies. This incident showed the gap between conventional insurance coverage and the real risks faced by businesses today. The numbers tell an even more compelling story: the average cost of a data breach in 2024 has reached $4.88 million, while mega-breaches affecting 50-60 million records can cost up to $375 million.
Cyber insurance is a specialized insurance that protects businesses from internet-based risks, including data breaches, ransomware, and cyberattacks. It provides first-party coverage for direct losses such as business interruption and data recovery, and third-party coverage for liabilities like customer lawsuits and regulatory fines. Modern cyber insurance policies also address emerging risks from cloud services, remote work, and interconnected supply chains.
Coverage and Protection
Cyber insurance offers two main types of protection. First party coverage and third-party coverage. First party coverage addresses direct losses that a business suffers from cyber incidents. When a cyber attack forces operations to stop, this coverage helps cover lost income during the downtime. For example, if an e-commerce site goes offline due to a denial-of-service attack, the policy might cover lost sales during the outage period.
Data recovery is another aspect of first party coverage. When hackers destroy or encrypt company data, the insurance can pay for retrieving or rebuilding that information. This is particularly important in cases of ransomware attacks, where critical business files are locked away until a ransom is paid. The coverage extends beyond just the technical aspects of data recovery. It usually includes the costs of crisis management and legal advisors to guide compliance with notification laws.
The notification process itself is another significant expense that cyber insurance can cover. When customer data is compromised, businesses are required by law to notify affected individuals. This process involves sending notification letters, setting up call centers to handle inquiries, and providing credit monitoring services to affected customers. Without insurance, these costs alone could ground a small or medium-sized business.
Third-party coverage on the other hand extends protection beyond the insured organization to address claims made by customers and others affected by the cyber incident. This especially important when customers sue because their personal information was exposed. The insurance covers legal fees and settlements.
The Need for Coverage
Many small business owners believe they’re too small to be targets and this thinking has proven to be dangerous. Cybercriminals many times target smaller companies because they tend to have weaker security measures in place. Healthcare organizations handle sensitive patient data protected by strict regulations, and a breach can result in heavy fines and lost trust.
Medical facilities need coverage that covers both data protection and patient care interruption. Similarly, financial services companies process countless transactions and store sensitive financial data, requiring comprehensive coverage for both cyber attacks and financial fraud. Retail companies store customer payment information and rely heavily on e-commerce systems. Their coverage needs to address payment card industry fines and customer notification costs after breaches. The retail sector has seen some of the most publicized breaches, with millions of customer records exposed and millions of dollars in damages. In 2023, over 10 million JD sports customers’ personal information, including names, addresses, phone numbers, and the last four digits of credit card numbers got exposed.
The Cost Factor
The cost of cyber insurance varies significantly based on several interrelated factors. Business size plays a major role – larger organizations typically pay more because they have more data to protect and more points of vulnerability. However, size isn’t the only determining factor. Industry type significantly impacts premiums, with healthcare and financial services often paying more due to the sensitive nature of their data and strict regulatory requirements. Security measures implemented by a business can significantly affect their premiums. Organizations with strong security practices often qualify for lower premiums, similar to how home security systems can reduce home insurance costs. These measures include regular security training for employees, updated security systems, well-documented incident response plans, and regular security assessments.
Claims history affects premiums just as it does with other types of insurance. Previous cyber incidents can increase premiums, but businesses can often reduce these costs over time by showing improved security practices and incident-free periods.
The Insurance Process
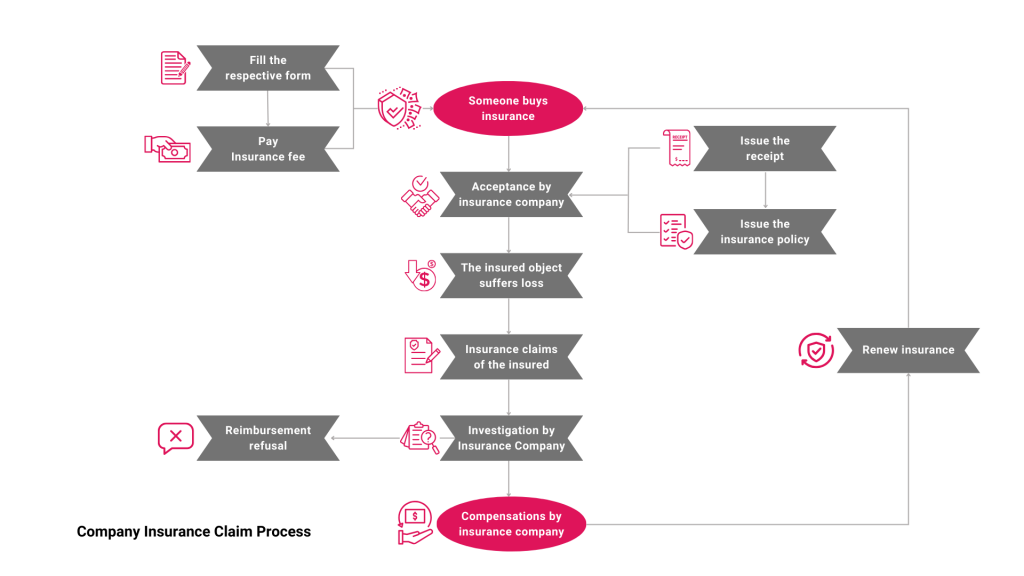
Obtaining cyber insurance begins with a detailed assessment of an organization’s cyber risks. Insurance providers examine current security practices, including network security measures, data backup procedures, employee training programs, and incident response plans. They also evaluate the types of data handled, business operations, previous security incidents, and industry-specific risks.
When cyber incidents occur, timing becomes very important. Businesses must document the incident, contact their insurance provider, follow their incident response plan, and preserve evidence. Insurance companies then assess the incident, determine coverage, coordinate with response teams, and process payments for covered expenses. Not everything falls under cyber insurance coverage. Standard policies typically exclude incidents that started before the policy began, damages resulting from poor security practices or ignored vulnerabilities, hardware damage from physical causes rather than cyber attacks, and costs to improve security systems after an incident.
Working with Cyber Insurance
Smart preparation helps businesses make the most of their coverage. This starts with maintaining detailed records of security measures, system configurations, data handling procedures, and security training programs. Regular updates to security systems, software patches, emergency contact lists, and response plans ensure the organization remains protected and compliant with policy requirements.
During an incident, quick and appropriate action are expected. Companies should follow their established incident response plans and maintain clear communication with insurers about incident details, response actions, and recovery progress. After an incident, there is the need to conduct thorough reviews to analyze what happened and update security measures accordingly. This process helps prevent similar incidents and may lead to adjustments in insurance coverage based on newly identified risks or changes in business operations.
Future of Cyber Insurance
The cyber insurance industry will continue to adapt to cyber threats changes. Insurance providers are adding coverage for new areas of risk, including remote work vulnerabilities, cloud service interruptions, Internet of Things devices, and artificial intelligence systems. These changes reflect the expanding digital footprint of modern businesses and the new risks being faced. Insurance companies are also raising their requirements for coverage. They increasingly require stronger security measures, regular security assessments, comprehensive employee training programs, and detailed incident response planning. These requirements help reduce risk for both the insurer and the insured while promoting better cybersecurity practices.
Modern Business Considerations
Supply chain connections create additional complexities for cyber insurance. Modern businesses depend on various suppliers and partners. Each of these is a potential point of vulnerability. Cyber insurance must account for vendor security requirements, partner system connections, data sharing agreements, and third-party access controls.
Cloud services is another layer of consideration for cyber insurance. As businesses migrate more operations to the cloud, insurance needs to address service interruptions, data storage issues, access problems, and provider security gaps. The shared responsibility model of cloud computing creates new questions about liability and coverage that insurance providers must address.
Mobile devices and remote work have expanded the traditional security perimeter, requiring insurance to cover remote access security, device management, data protection, and communication security. This expansion of the work environment has created new vulnerabilities that organizations must address and insurers must cover.
Making Informed Decisions
When selecting cyber insurance, businesses should carefully assess their specific needs and risks. This means understanding what data they handle, which systems are critical to their operations, what regulations apply to their business, and what specific risks they face. This assessment helps ensure the selected coverage adequately protects the organization’s most important assets and operations.
Organizations should review different coverage options while paying careful attention to exclusions and coverage limits. Industry requirements and regulations may dictate certain coverage elements, making it important to understand these requirements when selecting a policy.

