What is Data Loss Prevention?
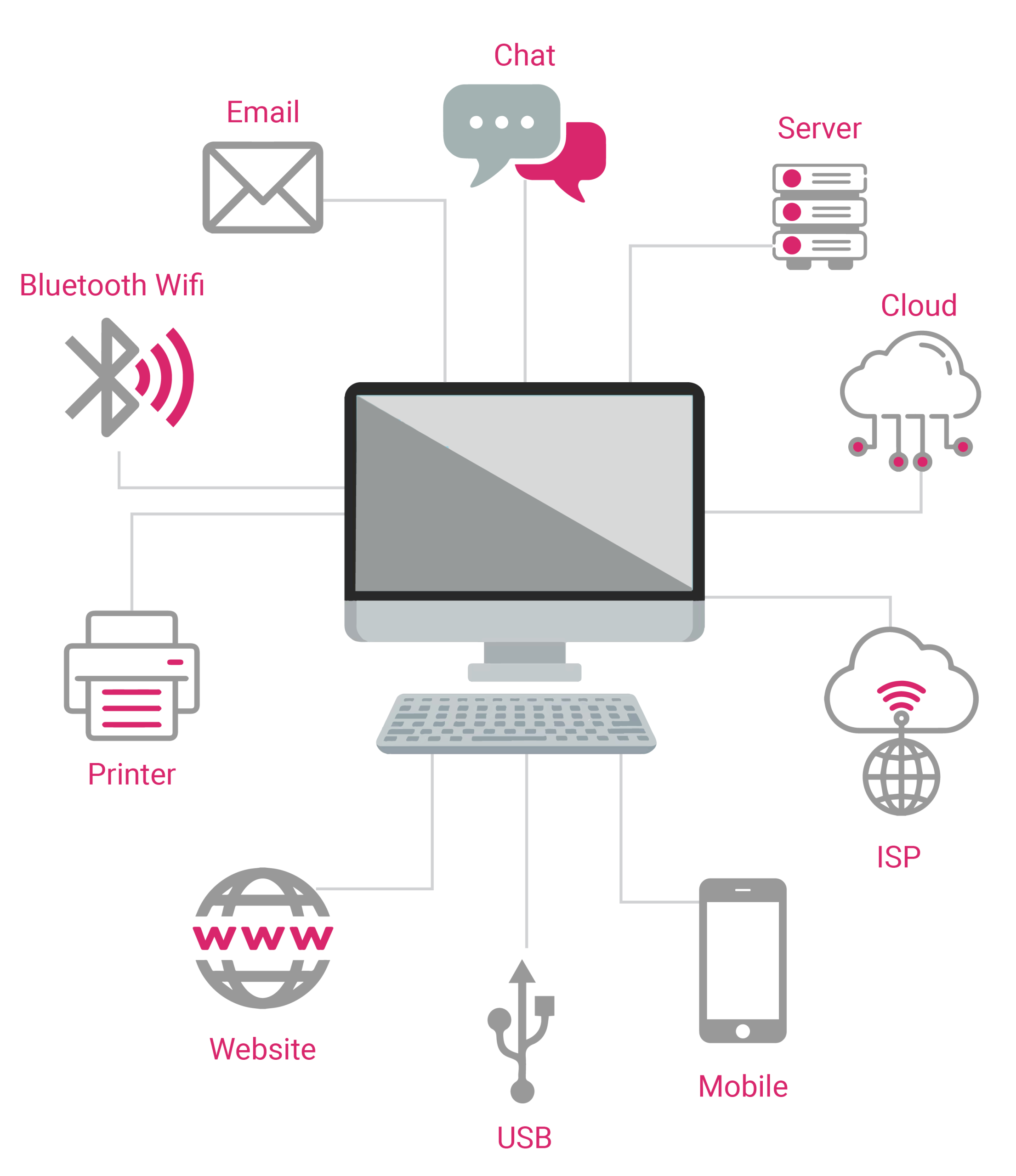
Data Loss Prevention are the strategies, tools, and practices that organizations use to detect and prevent unauthorized access, use, or transmission of sensitive data. DLP is like a comprehensive security system for your data. Just as a home security system monitors doors and windows, DLP keeps track of all the ways data might leave your organization. Emails, USB drives, cloud uploads, network transfers – everything. When it spots something suspicious, it can alert security teams or even stop the action automatically.
Data Loss Prevention (DLP) refers to strategies, tools, and practices used by organizations to detect and prevent unauthorized access, use, or transmission of sensitive data. DLP protects data in all states—at rest, in transit, and in use—by monitoring movement, enforcing security policies, and blocking or alerting on suspicious activities. It addresses risks from human error, insider threats, and cyberattacks, ensuring compliance and safeguarding critical information assets.
What is Data Loss Prevention?
The need for DLP becomes very obvious when we look at the numbers. According to recent IBM research, the average cost of a data breach now exceeds $4.88 million. The loss is not only money – businesses also face damage to their reputation and loss of customer trust.
Lets consider these case studies:
- A healthcare worker accidentally emails patient records to the wrong address
- An employee downloads sensitive customer data before leaving for a competitor
- A cybercriminal uses stolen credentials to access and extract proprietary information
- A staff member uploads confidential documents to their personal cloud storage
Each of these situations could lead to serious consequences. DLP systems help prevent such incidents by monitoring data movement and enforcing security policies.
The Three States of Data
- Data at Rest: Information stored in databases, file systems, or cloud storage
- Data in In transit: Information moving through the network, being sent via email, or transferred to external devices
- Data in Use: Information being accessed, processed, or modified by users and applications

A good DLP solution must protect data in all these states. For example, when data is at rest, DLP systems should ensure only authorized users have access. When data is in motion, they can encrypt sensitive information or block unauthorized transfers. For data in use, they can prevent actions like copy-paste or screen captures of sensitive information.
Common Causes of Data Loss
Human Error
People make mistakes. An employee might accidentally:
- Send sensitive information to the wrong recipient
- Leave a laptop containing confidential data in a public place
- Upload private documents to a public cloud folder
- Share access credentials with unauthorized persons
Insider Threats
Sometimes, the danger comes from within. Employees or contractors with access to sensitive data might:
- Take company data when leaving for a competitor
- Sell confidential information to third parties
- Share trade secrets with unauthorized individuals
- Abuse their access privileges for personal gain
External Attacks
Cybercriminals constantly devise new ways to steal data:
- Phishing attacks to gain access credentials
- Malware that exfiltrates sensitive information
- Direct attacks on databases and storage systems
- Supply chain compromises that create backdoors
Key Components of DLP
Data Discovery and Classification
Before you can protect data, you need to know what you have and where it is. DLP systems help by:
- Scanning storage systems to find sensitive information
- Categorizing data based on its sensitivity level
- Creating inventories of protected information
- Identifying where high-risk data resides
Policy Creation and Enforcement
- Who can access specific types of information
- When and how data can be shared
- Which channels are approved for data transmission
- What actions require additional authorization
Monitoring and Detection
Continuous monitoring helps catch problems early:
- Real-time analysis of data movement
- Pattern recognition for suspicious activities
- Behavioral analysis to spot unusual access
- Automated alerts for policy violations
Response and Prevention
When issues are detected, DLP systems can:
- Block unauthorized data transfers
- Encrypt sensitive information automatically
- Alert security teams about violations
- Create audit trails for investigation
Types of DLP Solutions
Network DLP | Endpoint DLP | Cloud DLP |
|
|
|
Hardware-Based DLP Solutions
Recent advances have brought new approaches to DLP. For example, the our cyber-secure SSD implements security at the firmware level:
- AI-embedded monitoring tracks data access patterns
- Built-in sensors detect physical tampering attempts
- Real-time response to unauthorized activities
- Independent operation without relying on software updates
This hardware-based approach offers unique advantages:
- Cannot be disabled by software attacks
- Works even if the operating system is compromised
- Provides consistent protection without updates
- Responds faster to threats
Implementing a DLP program needs planning and execution. Organizations should begin with a thorough assessment of their current data environment. This means documenting all sensitive information and understanding storage locations. Additionally, rather than rushing to implement everything at once, start with the most critical data sets. This allows your team to test and refine policies before broader deployment. This approach also users time to adapt to new procedure.
Human Element of DLP
Regular training sessions should connect security procedures to daily work tasks, making it clear how data protection fits into normal operations. When users understand why data protection matters, they become active participants in the security process.
Artificial intelligence and machine learning bring new capabilities to DLP systems. These technologies improve threat detection accuracy and reduce false alarms that can frustrate users. They also help systems better understand the context of data usage. The balance between security and usability remains important. Technical solutions must be able to work alongside human activity.
Conclusion
A properly designed DLP program brings together people, processes, and technology to protect valuable information assets. It requires careful planning and consistent attention to both technical and human factors. This balanced approach helps ensure that data protection becomes a natural part of how everyone works, rather than an obstacle to productivity.

