The Health Insurance Portability and Accountability Act (HIPAA) Security Rule is one of the most significant regulations in healthcare data protection. It establishes national standards to protect individuals’ electronic personal health information that is created, received, used, or maintained by healthcare organizations. The rule requires proper safeguards to ensure the confidentiality, integrity, and security of electronic protected health information, commonly known as ePHI.
The HIPAA Security Rule sets national standards to protect electronic protected health information (ePHI) by requiring healthcare organizations and their business associates to implement safeguards ensuring confidentiality, integrity, and availability. It mandates administrative, physical, and technical measures, including risk assessments, access controls, and audit systems, to prevent unauthorized access, alteration, or loss of ePHI. Compliance also requires documentation, ongoing monitoring, and updates to security practices to address emerging threats.
Key Concepts and Definitions
Electronic Protected Health Information are health information that can identify an individual and exists in electronic form. This can be medical records, insurance details, billing information, test results, and appointment schedules. It covers any health-related data that can be linked to a specific person.
The Security Rule applies to two main categories of organizations. First are covered entities, which are basically healthcare providers like doctors, clinics, and hospitals, as well as health plans and healthcare clearinghouses. The second category are business associates—organizations that render services to covered entities and handle protected health information. These might be billing companies, cloud storage providers, electronic health record vendors, or IT service providers.
Foundation of Security
The Security Rule builds its requirements on three fundamental principles: confidentiality, integrity, and availability.
Confidentiality: This ensures that health information remains private and accessible only to authorized people. Healthcare organizations must implement various controls and procedures to prevent unauthorized access and disclosure of health information. This principle recognizes that patient trust depends on keeping sensitive health information private.
Integrity: Focuses on the accuracy and reliability of health information. Healthcare organizations need to implement systems and processes that prevent unauthorized alterations or destruction of ePHI.
Availability: Only authorized users can access health information when needed. This requires maintaining reliable systems for storing and processing health information while ensuring quick and dependable retrieval methods.
Administrative Safegaurds
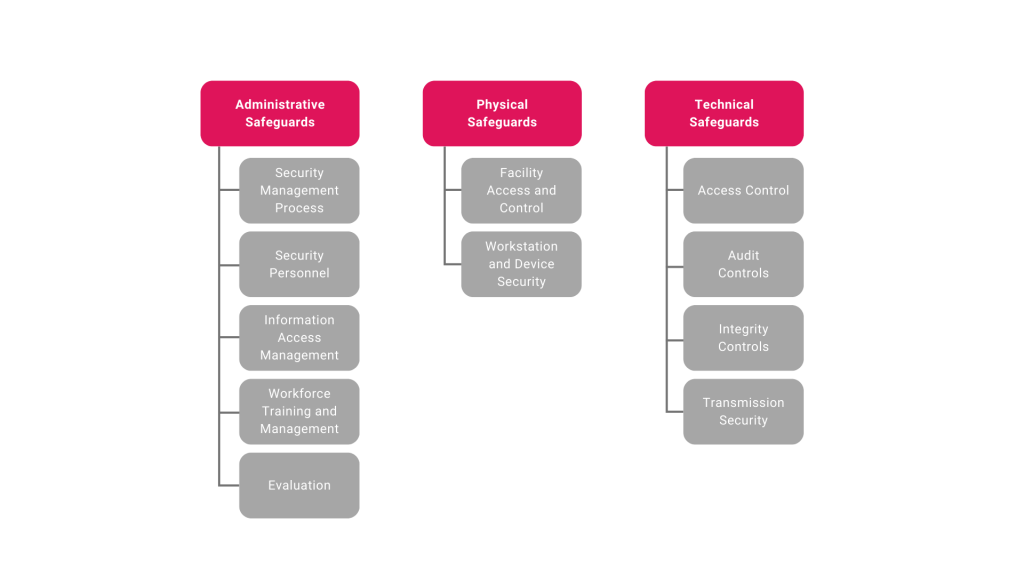
These measures include the policies, procedures, and actions organizations take to protect ePHI. A well-designed security management process begins with regular risk assessments to identify potential threats to ePHI. Organizations must then implement appropriate security measures to address these risks, create enforcement mechanisms for policy violations, and maintain ongoing system activity reviews.
Each healthcare organization needs dedicated security personnel responsible for developing and maintaining security policies. This individual or team oversees compliance with the Security Rule, responds to security incidents, and keeps security measures current with emerging threats. They work closely with other departments to ensure security measures support rather than hinder patient care.
Information access management is another critical administrative component. Organizations must carefully control who can access ePHI and under what circumstances. This includes establishing procedures for granting and removing access and conducting regular reviews of access permissions.
Physical Safeguards
Physical security measures protect the spaces and equipment where ePHI resides. Healthcare organizations must control physical access to their facilities through various security measures. This might be securing entry points and monitoring visitor access. These measures protect not only electronic systems but also the infrastructure that supports them.
Technical Safeguards
Technical security measures use technology to protect ePHI. Access control systems ensure that only authorized users can view or modify health information. These systems require unique identification for each user and include emergency access procedures for situations when normal authentication systems might be unavailable.
Audit controls allow organizations to monitor system activity and detect potential security incidents. These systems record and examine access attempts, track changes to health information, and maintain detailed logs of system usage. This information helps organizations identify and respond to security threats while also providing documentation for compliance purposes.
Practical Implementation
Implementing the Security Rule begins with a thorough risk assessment. You need to understand your current security situation before you can make improvements. This process involves identifying all systems that handle ePHI, mapping how data flows through the organization, and evaluating current security measures. The selection of security measures depends heavily on organizational characteristics. Small medical practices face different challenges than large hospitals and need security solutions that match their resources and capabilities. Technical infrastructure also influences security choices, as measures must work with existing systems and match staff expertise.
Cost is another important factor in security planning. Businesses need to balance security needs with available resources. This includes considering both initial implementation costs and ongoing expenses for maintenance and training.
Documentation and Maintenance
The Security Rule requires thorough documentation of all these security measures. Organizations must maintain written policies and procedures, risk assessment results, and records of security-related decisions. These documents provide guidance for staff and demonstrate compliance during audits.

