
An Advanced Persistent Threat (APT) is a long-term, highly sophisticated cyberattack in which an adversary gains continuous, unauthorized access to a network while actively avoiding detection. APT groups use customised malware, stealth techniques, and targeted tactics—often through social engineering or zero-day exploits—to move laterally, monitor activity, and extract sensitive data. These operations are typically backed by nation-states or organised groups and focus on strategic objectives such as espionage or intellectual property theft.
Characteristics of an APT
APTs are not casual threats—they require a high level of expertise and dedication from attackers. These entities often involve teams of skilled hackers backed by significant resources, sometimes sponsored by nation-states or organized criminal groups. Their distinguishing traits include:
- Long-Term Access: The attackers remain embedded within the targeted system for extended periods, conducting surveillance, gathering data, and deploying carefully planned tactics.
- High Customization: APTs are tailored to exploit specific vulnerabilities in their targets, ensuring maximum impact with minimal chance of discovery.
- Stealthy Operations: These attacks avoid detection by blending in with regular network traffic and employing techniques like encryption and obfuscation.
- Strategic Objectives: Their goals often align with espionage, economic sabotage, or competitive advantage, targeting sectors like finance, defense, healthcare, and technology.
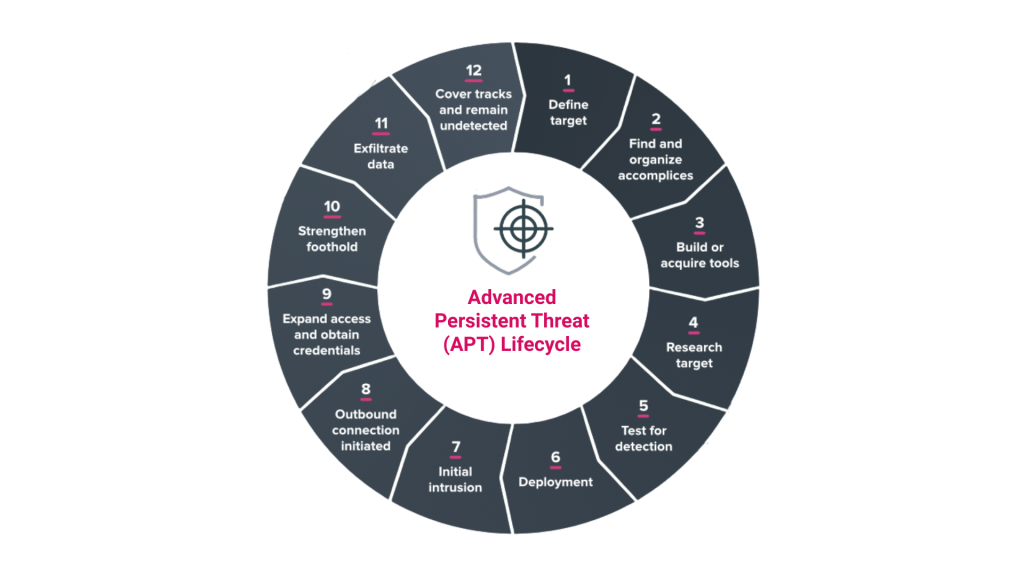
How Advanced Persistent Threats Operate
The operation of an APT typically unfolds in a series of calculated steps. These steps are designed to ensure seamless entry, deep penetration, and continued persistence within the target system.
Phase 1: Initial Entry
APTs often begin with social engineering tactics or spear-phishing campaigns. These methods rely on exploiting human vulnerabilities—sending well-crafted emails containing malicious links or attachments that deceive users into granting system access. Sometimes attackers leverage zero-day vulnerabilities to enter undetected.
Phase 2: Establishing Presence
Once inside, attackers install malware or backdoors that allow them to maintain access. These tools often include remote access Trojans (RATs) or custom scripts tailored to the target environment. During this phase, attackers ensure their presence is hidden by blending their activities with legitimate processes.
Phase 3: Lateral Movement
With access established, APT actors navigate through the network, seeking privileged accounts and sensitive systems. This lateral movement involves escalating privileges, hopping across machines, and mapping the entire system architecture.
Phase 4: Data Exfiltration
The ultimate aim of most APTs is to steal valuable data. Attackers identify and extract information that aligns with their objectives, transferring it outside the network while avoiding detection.
Phase 5: Persistence
Advanced Persistent Threats earn their name from their ability to remain active over long periods. Even when discovered and countered, they may return through alternate channels or exploit previously implanted vulnerabilities.
Known Examples of APT Incidents
- Operation Aurora (2010): This attack targeted major corporations like Google and Adobe, compromising intellectual property and sensitive business information.
- APT1 Campaign: Believed to be linked to a state-sponsored group, this prolonged operation targeted companies across multiple industries for economic espionage.
- Stuxnet Worm: While not a traditional APT, this advanced cyber weapon infiltrated industrial control systems, demonstrating the devastating effects of persistent threats.
Preventive Measures Against APTs
Mitigating the threat of Advanced Persistent Threats requires a proactive approach. Key strategies include:
- Network Segmentation: Dividing the network into smaller, isolated zones makes it harder for attackers to move laterally.
- Regular Patch Updates: Closing known vulnerabilities is crucial in preventing entry.
- Endpoint Monitoring: Continuous tracking of system behavior helps identify unusual activities indicative of APT actions.
- Strong Authentication Protocols: Implementing two-factor authentication and encryption strengthens access controls.
- Employee Training: Educating staff on recognizing phishing attempts and other forms of social engineering reduces the likelihood of initial compromise.
Advanced Hardware Solutions in APT Defense
Modern cybersecurity solutions increasingly integrate hardware-based measures to detect and prevent APT activities. Devices equipped with AI-embedded security systems offer real-time monitoring of data access patterns, helping identify anomalies before they escalate. For example:
- AI-Powered SSDs: These drives include embedded sensors capable of detecting physical tampering alongside firmware-level anomaly detection. By securing all data streams through a single entry point, such devices minimize vulnerabilities.
- Dynamic Threat Responses: Advanced hardware can autonomously shut down access or purge sensitive data when irregularities arise, providing immediate containment during an attack.
The Importance of Vigilance in APT Defense
Advanced Persistent Threats require constant attention and adaptability to counter their evolving tactics. Cybersecurity teams must maintain a culture of vigilance, regularly reviewing system logs, updating access protocols, and conducting penetration tests to uncover weaknesses.

