What is Data Encryption?
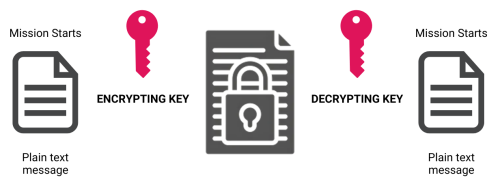
When you type a message or save a file on your computer, it exists as “plaintext” – information anyone can read. Encryption takes this plaintext and uses special mathematical formulas (algorithms) and a unique key to turn it into “ciphertext” – scrambled content that appears random and meaningless to anyone without the right key to decode it.
Data Encryption is the process of converting readable information (plaintext) into scrambled, unreadable data (ciphertext) using mathematical algorithms and keys, ensuring that only authorized parties can access it. It protects sensitive information—such as financial data, personal messages, and business files—both when stored (at rest) and during transmission (in transit). Common methods include symmetric encryption, which uses a single key, and asymmetric encryption, which uses paired public and private keys for secure communication.
Why We Need Encryption
We share vast amounts of sensitive information online every day:
- Credit card numbers when shopping
- Personal messages and emails
- Medical records
- Business documents
- Banking information
- Private photos and files
Without encryption, this data would be exposed to anyone who might intercept it. Hackers, cybercriminals, and other unauthorized parties could easily steal, read, or change your information. Encryption creates a strong barrier that keeps your data safe and private.
Types of Encryption
Symmetric Encryption: The Simple Key System
Symmetric encryption uses one key for both encrypting and decrypting data. It is similar to a single house key that both locks and unlocks your front door. When you want to share encrypted data with someone using symmetric encryption, you’ll need to find a secure way to give them the key.
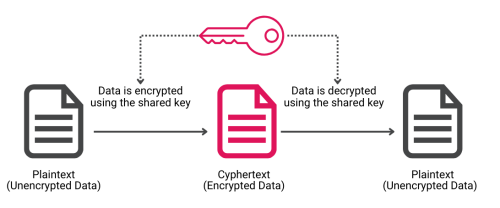
This method offers quick processing and works well for:
- Encrypting files on your personal devices
- Protecting data stored in databases
- Securing communication between two parties who have already exchanged keys
Popular symmetric encryption algorithms include:
Advanced Encryption Standard (AES): It is the current standard for symmetric encryption. The U.S. government adopted it to protect classified information, and it now secures countless applications worldwide. AES can use different key lengths (128, 192, or 256 bits) to balance security and speed.
Data Encryption Standard (DES) and Triple DES: While older and no longer recommended for new applications, these algorithms played an important role in encryption history. Triple DES applies the DES algorithm three times to increase security, but newer options like AES offer better protection.
Asymmetric Encryption: The Two-Key Approach
Asymmetric encryption uses two different but mathematically related keys – a public key for encryption and a private key for decryption. The public key can be freely shared with anyone, while the private key must be kept secret by its owner.
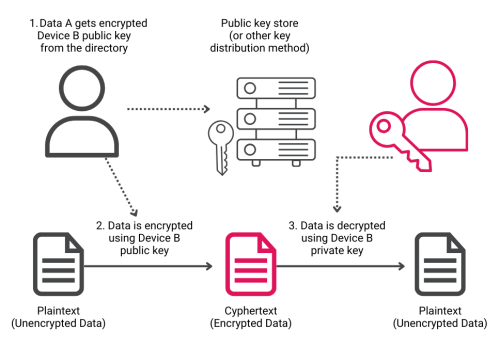
This system solves a key problem in encryption: how to securely share keys over insecure networks. With asymmetric encryption, you can:
- Send encrypted messages to someone using their public key
- Digitally sign documents to prove your identity
- Establish secure connections with websites
- Create secure communication channels between parties who have never met
Common asymmetric encryption algorithms include:
RSA (Rivest-Shamir-Adleman): Named after its creators, RSA remains one of the most widely used asymmetric algorithms. It is in fact the backbone of many secure internet communications and digital signature systems.
Elliptic Curve Cryptography (ECC): ECC provides strong security with shorter key lengths than RSA, making it ideal for mobile devices and other systems where processing power or storage might be limited.
Protecting Data at Rest and in Transit
Data needs protection in two main states: when it’s being stored (at rest) and when it’s being sent (in transit). Different encryption methods and protocols ensure security in both situations.
Data at Rest
When information sits stored on a device or in the cloud, encryption prevents unauthorized access even if someone physically steals the storage medium. Examples include:
- Full Disk Encryption: This method encrypts entire storage devices, protecting all data on your computer or phone. If someone steals your device, they can't access your files without the encryption key.
- File-Level Encryption: Individual files or folders can be encrypted separately, allowing more granular control over what's protected and who can access it.
- Database Encryption: Organizations can encrypt specific columns or entire databases to protect sensitive information while maintaining usability for authorized users.
Data in Transit
Information traveling between devices or over networks needs special protection to prevent interception. Several protocols and methods ensure secure transmission:
- Transport Layer Security (TLS) TLS protects data as it moves between web browsers and servers. When you see "https://" in your browser's address bar, TLS encryption is active, creating a secure tunnel for your data.
- Virtual Private Networks (VPNs) VPNs encrypt all data traveling between your device and the VPN server, hiding your internet activity from anyone who might be watching.
Encryption Standards and Best Practices
Standard algorithms and protocols guide the proper use of encryption across different systems and applications. These standards ensure that encryption remains effective and compatible across various platforms.
The Gold Standard AES-256 is the highest level of symmetric encryption widely used today. The “256” refers to the key length in bits – longer keys make the encryption harder to break. Many security-focused organizations require AES-256 for protecting sensitive data.
Management of Encryption keys need careful handling. Poor key management can compromise even the strongest encryption. Organizations should:
- Store keys separately from encrypted data
- Keep backup copies of keys in secure locations
- Regularly update and rotate keys
- Limit key access to authorized personnel
- Document key handling procedures
Hardware-Based Encryption Solutions
Modern devices often include specialized hardware for encryption. These solutions offer advantages over software-only approaches:
Hardware Security Modules (HSMs): These dedicated devices manage and protect encryption keys. Banks and other financial institutions use HSMs to secure sensitive transactions and maintain regulatory compliance.
Self-Encrypting Drives (SEDs): SEDs handle encryption at the hardware level. For example, the X-PHY® AI-embedded cyber-secure SSD implements security features directly in its firmware. This approach offers several benefits:
- Built-in sensors detect physical tampering attempts
- AI-driven systems monitor data access patterns
- Real-time threat response without manual intervention
- Protection against both known and unknown cyber threats
The integration of artificial intelligence with hardware encryption creates an autonomous security system that operates 24/7 without requiring updates or human oversight.
The Future of Encryption
Quantum Computing: Traditional encryption may become vulnerable to quantum computers. Researchers are developing quantum-resistant algorithms to ensure continued security.
AI and Machine Learning: Artificial intelligence enhances encryption by:
- Detecting unusual access patterns
- Predicting potential security threats
- Automating security responses
Zero-Trust Architecture: Modern security approaches assume no inherent trust. Every access attempt requires verification, with encryption playing a central role in protecting data at all points.
The impact of encryption extends beyond just keeping data secret. It helps maintain data integrity, verify user identities, and ensure regulatory compliance. As we adopt more and more of technology in our daily lives, encryption remains fundamental to protecting our information and privacy.

