
Threat hunting means actively searching for signs of unwanted activity in computer systems. Instead of waiting for an alarm, threat hunting requires experts to study every detail of regular system behavior. In this article, we explain what threat hunting is, how it helps in keeping data secure, and how devices with built-in sensors and real-time monitoring contribute to a better defense.
Threat hunting is the proactive process of examining network data, system logs, and hardware sensor outputs to identify hidden or emerging security threats before automated alerts are triggered. It combines human expertise with machine-driven analysis to compare real-time activity against established behavioural baselines and detect anomalies that may signal intrusion. Modern hardware-based security, including devices with built-in sensors and real-time monitoring, strengthens threat hunting by providing continuous, tamper-resistant visibility into both digital and physical system conditions.
The Meaning of Threat Hunting
Threat hunting is the practice of searching through data records, sensor readings, and other signals within a network to find unusual activities. It does not rely on alarms triggered by known hazards. Experts use historical records of normal behavior as a guide. They compare these records with the current messages from the network. Even a small change might hint at a hidden intrusion that has not yet made itself fully known.
Security teams work hand in hand with machines that record every bit of data. The process involves gathering information from multiple channels. This includes network traffic, logs from devices, and data from embedded sensors. When the system shows an unexpected shift, experts examine all available sources to determine if a breach is underway. The goal is to spot the unwanted activity before it develops into a full incident.
A Brief History of Threat Hunting
In the early stages, security measures mainly focused on known issues. Devices and systems sounded an alarm when they encountered familiar problems. Over time, attackers began to use methods that did not trigger these alarms. This led to a change in how security teams viewed their work. Instead of relying on preprogrammed alerts, experts started to study every detail in order to notice hidden signs of intrusions.
This change meant that experts began to study system logs manually, looking for small mismatches in behavior. As computers became faster and data became greater, machines were introduced to help go through large amounts of information. Over the years, the method has grown into a practice that combines both human knowledge and the strength of automated devices. Today, these methods are now a solid part of keeping systems safe.
Methods and Practices in Threat Hunting
When teams set out to search for hidden activity, they start by collecting data from every available source. This data includes information from network messages, internal logs, and outputs from hardware sensors. Experts first build a picture of what is normal in a system. They record expected details about file access, user actions, and the physical state of devices. With this reference in hand, they check each new record to see if anything differs.
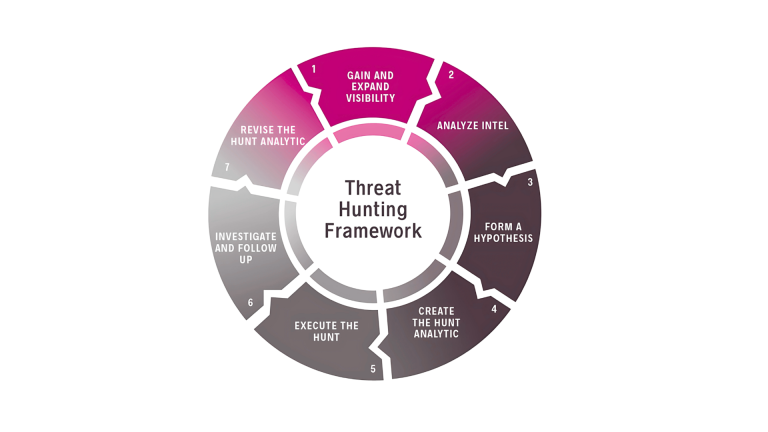
A typical threat hunting session is not random; it follows a pattern based on preparation and focused examination. Once the idea of what is expected is clear, teams begin to compare each new interaction against their records. The process may take place over long hours as every unusual detail is noted. Even a slight change in how data is read or written can suggest that someone is trying to break in. At this point, the system might raise an indicator that calls for further investigation.
A mix of manual review and automated filtering makes the process effective. Software tools review thousands of records to mark details that do not match the norm. Experts then closely check these records to confirm if the changes mean harm or if they are harmless shifts. It is this process of checking every piece of data that forms the heart of threat hunting.
The Role of Hardware-Based Security in Threat Hunting
Modern devices such as our X-PHY® GUARD include features that go beyond software logs. Our security solution add hardware sensors that study the physical condition of a device. Examples include temperature sensors that note any sudden changes, light detectors that watch for unexpected room conditions, and motion detectors that sense if a device is moved without approval.
It can act immediately if it recognizes changes in its surroundings. This type of hardware often holds a small intelligence within its firmware. The internal logic keeps track of every read and write action, while the sensors keep an eye on physical signs. In one design, all data flows through a single, secure channel.
When the device senses a light change in the room or a sudden shift in its own temperature, it may freeze its operations. In such an event, the device alerts the security team, which can then review the detailed records stored within its memory. This quick response is an extra check that even the smallest anomaly is not left unexamined.
Tools and Techniques Used by Analysts
Threat hunting makes use of various tools designed to check every part of a system. Devices with dedicated sensors, custom firmware, and programmed responses are part of the toolset. Some systems channel every data record through one secure door, making it easier to check every detail. When a sensor picks up a disturbance or a log file shows unusual content, the system acts without waiting for external instructions.
Often, these devices come with artificial intelligence designed to help check the flow of records in real time. They compare every new signal with what is stored as normal. When a clear difference appears, these systems can isolate the part of the network under attack. In this way, the extra help from trusted machines allows human experts to focus on understanding each alert and deciding on the best response. By using both smart hardware and detailed record checks, teams can keep track of every aspect of system behavior.
Threat Hunting in Larger Systems: Servers and Data Centers
In environments where large amounts of data move constantly, such as large servers or data centers, threat hunting must cover several layers. In these settings, extra devices are often installed to act as independent observers. They check every detail across both network messages and the physical condition of the hardware. Their work is separate from the main system, so they offer an honest view of the state of the overall network.
These devices look at ordinary activity throughout the entire system. Even slight differences in how files are accessed or stored quickly catch their attention. When they note a change, these devices can isolate the affected area while a team of experts studies the records. The detailed recording of every transaction, combined with outputs from physical sensors, provides a united effort against any unauthorized activity.
Because large systems gather huge amounts of data, the extra check provided by hardware plays a significant role. It is not enough to check only the digital signals. Many modern devices add layers of security by checking the physical condition near the hardware, such as temperature shifts or minor changes in the environment. This additional information gives security teams better insight when the records do not match the usual pattern. The comprehensive review of every detail helps to keep even the smallest unwanted activity in check.
Challenges and Advantages in Threat Hunting
Although the practice of threat hunting has many rewards, it also brings challenges. Examining a vast amount of records and sensor data requires careful thought and sound judgment. A system that produces many alerts could overwhelm a team if not properly tuned to ignore unimportant shifts. Finding the right balance between automated checks and careful review by experts is a constant task.
On the other hand, threat hunting gives organizations a way to keep a close eye on what happens in their systems. Because every detail is recorded and studied, the method helps to address unwanted activity at an early stage. The effort to check every detail may require extra time and resources, but the outcome is an environment where records are clear and safe. Each unexpected message or sensor output becomes soon a sign for further review. With every examination, the overall system gains clarity and the chances for unwanted events are reduced.
In keeping a close watch on every routine action, teams gain a record that offers guidance for future reviews. The care put into studying each detail builds an environment where every alert is taken as a sign that further review is needed. This steady work helps maintain safety and offers a clear basis for adjusting everyday procedures.

