Credentials are the keys to our email accounts, banking services, practically everything. These identifiers grant access to our most important information. Credential theft occurs when bad actors steal these keys – typically usernames, passwords, and other authentication data – to gain unauthorized access to systems and accounts.
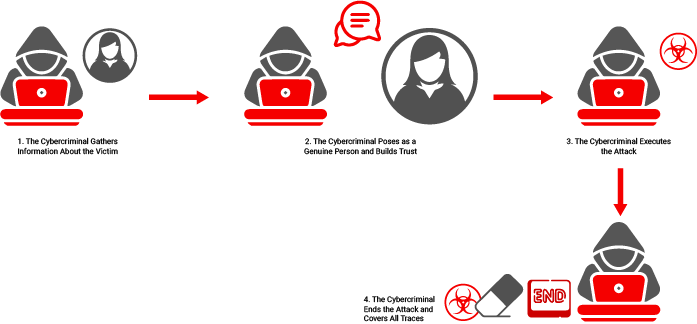
Credential theft occurs when attackers steal usernames, passwords, or other authentication data to gain unauthorized access to accounts and systems. Unlike other cyberattacks, it targets the human element, allowing attackers to bypass traditional security measures by appearing as legitimate users. Common methods include phishing, malware, and man-in-the-middle attacks, which can lead to financial loss, data breaches, and operational disruption.
What Makes Credential Theft Different?
Unlike other cyber attacks that focus on system vulnerabilities, credential theft targets the human element of security. When attackers obtain valid credentials, they can bypass traditional security measures because they appear as legitimate users. This makes credential theft particularly dangerous, as many security systems cannot distinguish between a legitimate user and an attacker using stolen credentials.
The Mechanics of Credential Theft
Phishing and Social Engineering:
Email remains the primary vector for credential theft. Attackers send messages that appear to come from trusted sources like banks, social media platforms, or workplace applications. These emails usually create a sense of urgency that intends to push recipients to act quickly without thinking. A bank fraud alert or an urgent message from a supervisor can make people overlook warning signs.
Malware-Based Theft:
Malicious software can record keystrokes, capture screen contents, or extract stored passwords from web browsers. This software often enters systems through seemingly innocent downloads or email attachments. Once installed, it can operate undetected for long periods, gathering credentials and sending them to attackers.
Man-in-the-Middle Attacks:
These attacks intercept communications between users and legitimate services. When someone connects to public Wi-Fi at a coffee shop or airport, attackers can position themselves between the user and the network. From this position, they can capture login credentials as they travel across the network.
The Business Impact
Financial Loss:
According to recent data, the average cost of a data breach involving stolen credentials reaches $4.88 million. This includes direct losses, recovery costs, and damage to reputation. For healthcare organizations, the impact is even greater – hospitals spend 64% more on advertising in the two years following a breach to rebuild their reputation.
Data Breaches:
Stolen credentials can lead to larger data breaches. Once attackers gain initial access, they can move through networks, accessing sensitive information and systems. The SolarWinds incident is a perfect example of how one set of compromised credentials can affect thousands of organizations.
Operational Disruption:
When organizations detect credential theft, they must reset passwords, review access logs, and sometimes shut down systems temporarily. This disrupts normal operations and affects productivity.
Modern Defense Strategies
Hardware-Based Security :
New approaches to credential protection go beyond traditional software solutions. For example, our technology implements security at the firmware level. This hardware-based approach monitors data access patterns directly and can detect unusual behavior that might indicate credential theft.
The advantage of hardware security is its independence from the operating system. Even if malware compromises the system, hardware-based solutions continues to function. These systems can:
- Monitor access patterns at the physical level
- Detect anomalies without relying on known threat signatures
- Respond to unauthorized activities in real-time
- Operate even when the main system is compromised
Multi-Factor Authentication (MFA):
MFA has become a standard defense against credential theft. It requires users to provide additional proof of identity beyond passwords. Even if attackers steal passwords, they cannot access accounts without these additional factors. This might include:
- Something they have (like a phone or security key)
- Something they are (biometric data)
- Something they know (a separate password or PIN)
Zero Trust Architecture:
Organizations now implement zero trust models that treat all access attempts as potentially hostile. This approach verifies every access request and limits access to only what’s necessary.
Impact of Credential Theft
In 2022, Marriott International faced a significant breach when attackers tricked an employee at a Marriott hotel in Baltimore into giving them access to their computer. They accessed approximately 20GB of data, including confidential guest information and credit card details.
Another notable case occurred at MGM Resorts in September 2023, where attackers used stolen credentials to breach the company’s systems. The attack forced MGM to shut down their computer systems across all their properties, affecting everything from hotel room keys to slot machines. The incident cost MGM an estimated $100 million in direct losses and significantly impacted their Las Vegas operations for several days.
Building Strong Defenses
Organizations need multiple layers of protection to guard against credential theft. Employee training is the most important of these defenses. At Microsoft, for instance, regular security drills test employees’ ability to spot phishing attempts. These exercises simulate real attacks, providing immediate feedback when employees make mistakes. This approach has reduced Microsoft’s susceptibility to phishing attacks by 50%.
Password policies have also advanced beyond simple complexity requirements. Instead of forcing regular password changes which most times leads to weaker passwords. Many organizations now focus on length and uniqueness. The National Institute of Standards and Technology (NIST) recommends passwords be at least 12 characters long and checked against lists of compromised credentials.
What Does the Future Hold?
As we look ahead, several technological developments promise to reshape credential security. Artificial intelligence already plays a dual role in this space. While security teams use AI to detect unusual login patterns and potential credential theft, attackers also use it to create more convincing phishing emails and automate their attacks. Companies like IBM use AI-powered systems to analyze billions of security events daily, identifying potential credential theft attempts before they succeed.
Biometric authentication is another technology gaining ground. Apple’s Face ID and fingerprint recognition have set new standards for convenient security, but concerns about biometric data storage and privacy are still a concern. The European Union’s GDPR specifically classifies biometric data as sensitive information requiring special protection.
A Comprehensive Security Strategy
A successful security strategy begins with understanding your organization’s specific risks and requirements. This means conducting thorough assessments of critical systems and understanding how employees interact with these resources.
The Human Element in Security
While technical solutions provide essential protection, human behavior still needed for success. Organizations must make security procedures straightforward and practical. Clear guidelines help employees understand their role in protecting credentials. Quick access to support when security questions arise prevents employees from bypassing security measures out of frustration.
Looking forward, organizations must stay alert to new threats while maintaining existing protections. This requires ongoing attention to emerging attack methods, new security technologies, and changes in user behavior. Success comes from finding the right balance between security requirements and practical usability.

