
What is Social Engineering?
Social engineering is a sophisticated approach to cybersecurity threats that targets the most variable component of any system – people. Instead of battling firewalls or encryption, these attacks manipulate emotions, trust, and the predictability of human responses. Basically, these attacks exploit human psychology.
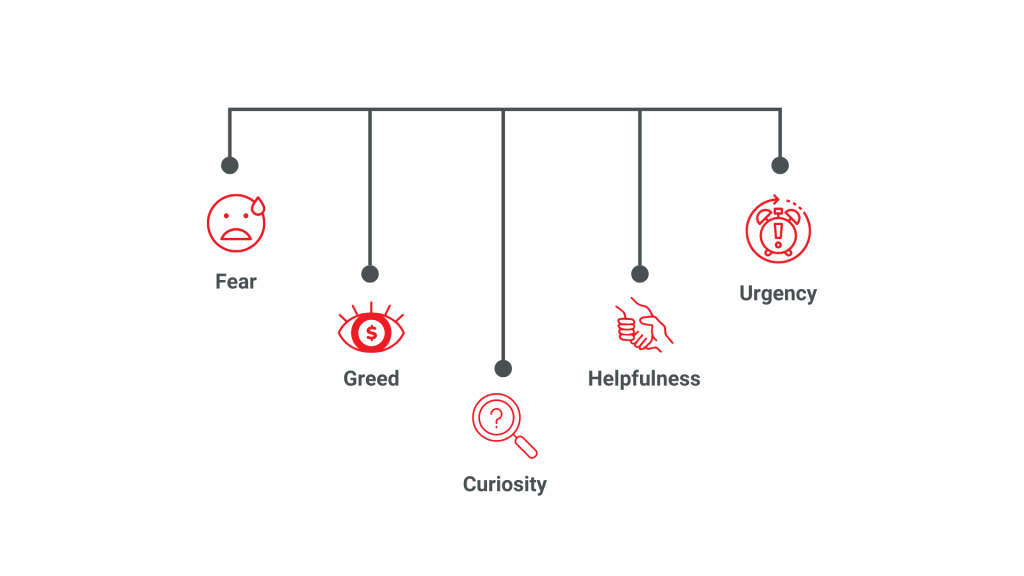
It is a manipulation tactic that exploits psychological triggers to breach security systems. Attackers hunt for emotional entry points. They understand that humans are driven by fundamental needs: curiosity, helpfulness, fear, and the desire to be appreciated or avoid trouble.
Social engineering is a cybersecurity threat that targets human psychology rather than technical systems, manipulating emotions such as fear, curiosity, or urgency to trick individuals into revealing sensitive information or granting unauthorised access. Common methods include phishing, impersonation, and other tactics designed to bypass rational decision-making. Effective defence requires verification, awareness training, and layered security controls to reduce the risk of manipulation.
The concept even predates technology as we know it. Con artists, confidence tricksters, and spies have used psychological manipulation for centuries. What changed was the scale and sophistication enabled by modern systems. Technology turned traditional confidence tricks into cyber strategies that can impact millions of victims at the same time.
A phishing email for instance might appear to come from a trusted bank. It will create an immediate sense of urgency. The message might suggest your account will be suspended unless you click a link and “verify” your information. The trick here is to tap into peoples anxieties about money making rational thinking difficult at that specific moment.
Common Tactics in Social Engineering
Social engineering attacks are never random. They follow careful psychological scripts designed to bypass your ability to think critically. Phishing is still the most prevalent technique, where attackers masquerade as legitimate entities to extract sensitive information, with an estimated 3.4 billion spam emails sent every day.
Emotional Manipulation Techniques
Attackers use many emotional strategies. Fear is used a lot – messages suggesting imminent account closure or legal action can scare people into immediate action. Curiosity is another powerful trigger. Intriguing subject lines or seemingly exclusive offers can trick people to click malicious links.
Another critical psychological pressure point is urgency. These actors give you a limited time offer or immediate consequences. They use this to reduce your ability to think critically. A message claiming “Your account will be locked in 10 minutes” triggers an instinctive fight-or-flight response, bypassing rational analysis.
Impact and Consequences
The stakes are far bigger than your personal inconvenience. Organizations face a huge financial and reputational risks from successful social engineering attacks. A single compromised employee credential can provide attackers needed access to your network.
During global health events like the COVID-19 pandemic, these attacks dramatically increased. Cybercriminals exploited widespread uncertainty and created phishing campaigns disguised as health alerts or government communications.
Prevention and Defense Strategies
Defending against social engineering needs a holistic approach that combines technological solutions with human education. Technical measures like multi-factor authentication provide essential barriers, but comprehensive staff training is still very paramount. Effective training programs should focus on developing psychological awareness. It should teach employees to recognize manipulation tactics and understand emotional triggers.
Key Defense Mechanisms
Verification is the primary defense. Before responding to urgent requests, you should:
- Independently confirm communication sources
- Contact organizations through official channels
- Avoid clicking unsolicited links
- Question unexpected communications
The fact is technology alone cannot guarantee protection. We remain both the weakest link and the most adaptable defense mechanism. Our ability to recognize patterns, feel empathy, and make intuitive judgments can be both a vulnerability and a powerful protective tool. Advanced artificial intelligence and machine learning technologies are increasingly being developed to help detect and prevent social engineering attacks. These tools are able to analyze communication patterns, identify anomalies, and provide alerts in real time. But our intuition and critical thinking is irreplaceable.
Conclusion
As technologies advance, so do social engineering tricks. Attackers continuously refine their methods. They use new communication platforms and understanding of how you think to exploit you. What worked five years ago might seem primitive compared to current sophisticated techniques.
Cybersecurity experts must adopt a proactive, adaptive mindset. This means continuous learning and staying updated on emerging threats.
Knowledge is the most powerful defense. When people understand how attackers think, manipulate, and operate, they become significantly harder to deceive. Education, awareness, and a healthy dose of skepticism turns potential victims into informed defenders.

